Google Play Store has been found harboring another malware and this one has the ability to disable the security settings on Android devices. The malware is doing this so that it would be able to perform different malicious tasks in the infected system’s background undisturbed.
You might be wondering what’s so interesting about another malware that’s hiding in the Play Store and probably trying to infect whatever it can. Well, for one, it was smart enough to slip past the Google security measures. It managed to do this by entering into a clean app and then become malicious.
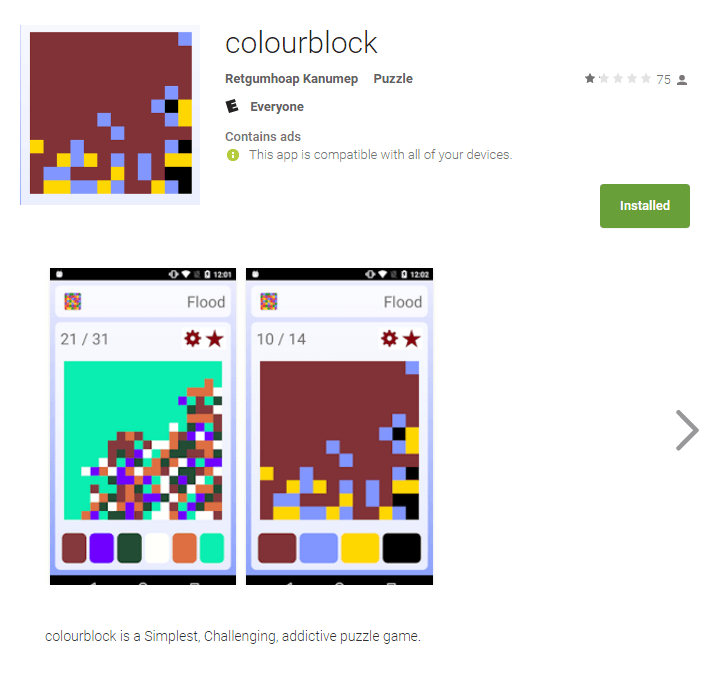
It was Kaspersky Lab’s researchers who discovered the malware and according to them it was hiding behind a certain puzzle game named ‘colourblock.’ Before the app was found to be malicious, there were over 50,000 downloads of it.
The Android-rooting malware itself was named Dvmap and it can disable security on the systems it infects. It does so to download another infected app which comes from a third-party source, one with less protection than the Play Store. It then injects its malicious code even in the device system runtime libraries. After that, it gains root access and removing it becomes harder than ever.
The newly discovered Dvmap can infect both 32-bit, as well as a 64-bit version of the device. After gaining root access, malware would try and install several different modules which even includes a few written in Chinese. Also, it installs the malicious application named “com.qualcmm.timeservices.”
It overwrites the runtime libraries of the infected system so that the module would be executed with system rights. With the goal of completing the started installation, this Trojan will turn off the feature called ‘Verify Apps’, and it’ll modify the system settings. The new modifications will ensure that installation of apps from the third-party sources would be allowed.
It’s this third-party app that’s to be blamed for connecting the infected device to the C&C server of the attacker. Upon making the connection, the hackers responsible will get full control of the phone.
It’s yet to be seen what kind of files will be executed, and will they be malicious or advertising in nature.
For now, the malware is still being tested. Meanwhile, the users who’ve downloaded the originally infected puzzle game are advised to back up the device’s data and then perform the factory data reset.
Additionally, watch out for such fishy apps so that you would avoid malware infections. They can be found even in the Google’s Play Store, so caution is highly advised as well as the strict use of trusted brands only.
You should check and verify the permissions given to the app before the installation and only grant permissions to those that don’t ask for suspicious things. Lastly, a good antivirus will serve as a decent protection and it will spare you from dealing with such problems.
DDoS attacks are increasing, calculate the cost and probability of a DDoS attack on your business with this DDoS Downtime Cost Calculator.





