The group behind this Android spyware is APT-C-23 that has been targeting Palestine and other countries in the Middle East for the last couple of years.
With multiple black hat groups existing, cybersecurity researchers track them to learn more about their respective patterns. This not only helps in fighting future threats but also offers greater insight into the motives of each group.
Keeping this in mind, a threat actor named APT-C-23/Two-tailed Scorpion is known for basing its targets in the Middle East using Windows and Android run malware.
It is worth noting that in April 2018 the same group was caught using Android malware called ViperRAT against Palestinians. At that time, ViperRAT was being distributed from Play Store.

Recently, however, researchers from ESET have found that the Android version of the spyware is starkly different from previous versions marking a shift in its capabilities.
See: Shoe give away scam hits Android users with malware on Play Store
Known as Android/SpyC23.A; the previous version included features such as the ability to take photos, download/delete files, uninstall applications, steal SMS messages, contacts, and sim credit balances. Now, the new one has extended features in addition to the previous ones enabling it to do the following things which weren’t possible before:
- Recording a user’s calls
- Recording a user’s screen
- Reading notifications from messaging apps
- Closing any notifications that are received from security apps installed such as an anti-virus app.
It does so by seeking user permissions when it is being installed. Since no user would consciously give such access, the malware uses technical jargon in order to confuse users. An example is shown below where it gets permission to read user notifications by calling it “Messages Encryption.”
Such functionality can allow an attacker to completely observe what a user is doing and is a huge breach of one’s privacy. Furthermore, by using the obtained data, these attackers can ultimately not only hijack a user’s online accounts but also blackmail them with their personal photos and messages.
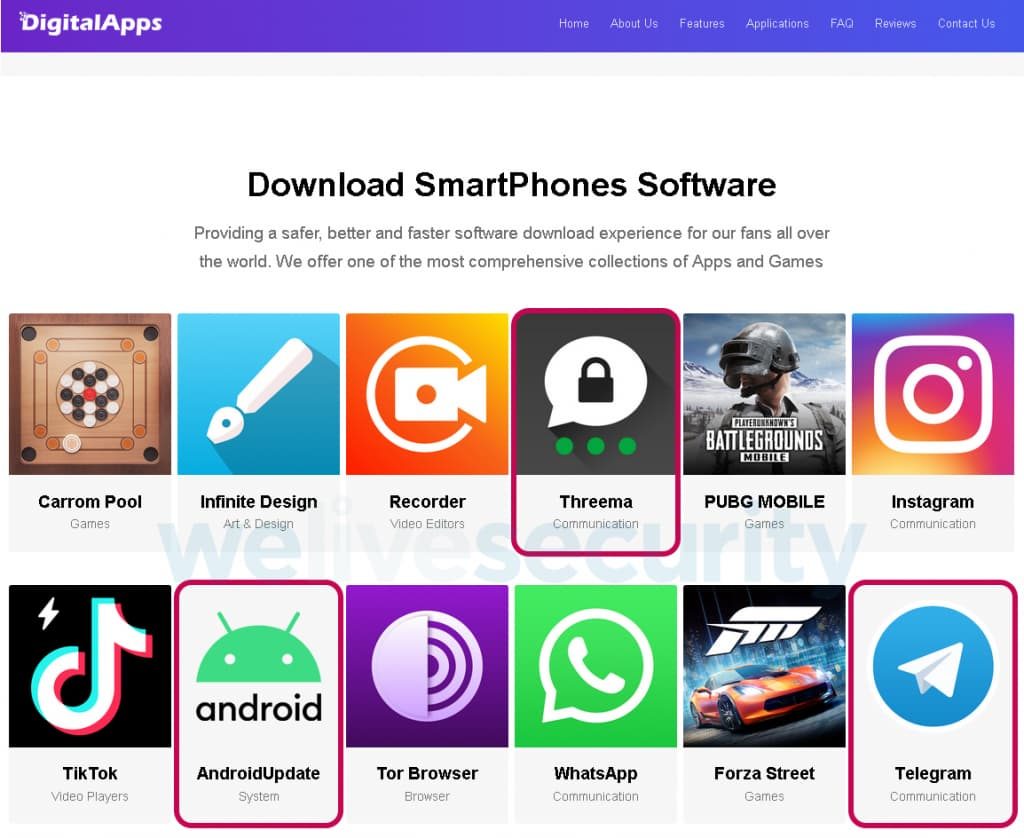
On the other hand, the malware is installed by trapping users through fake app stores such as “DigitalApps” in which malicious apps are available as shown below in conjunction with legitimate apps as well.
These malicious apps may pose highly downloaded ones such as Telegram or Instagram which makes it easy to convince users in downloading them.
If someone wanted to download one such app though, a 6 digit coupon code was sought which according to the researchers suggests that the attackers may be wanting to keep a low-profile by only allowing their selected targets to download the malware.
To conclude, we are still expecting to see further updates to this spyware which should make users take precautions in order to avoid being a victim. A good way to do so is by refraining from downloading unnecessary apps, keep in eye on what you are downloading from Google Play and third-party app stores.
Keep your device updated, install a reliable anti-malware solution, and carefully analyze the permissions an app is asking for.
Did you enjoy reading this article? Do like our page on Facebook and follow us on Twitter.