On the normal surface web that we use in our day to day lives, web hosting companies offer services that enable individuals and companies to host websites. The same goes for the dark web except that the hosting companies present there are not as well established and may not be able to afford cybersecurity professionals to monitor for vulnerabilities.
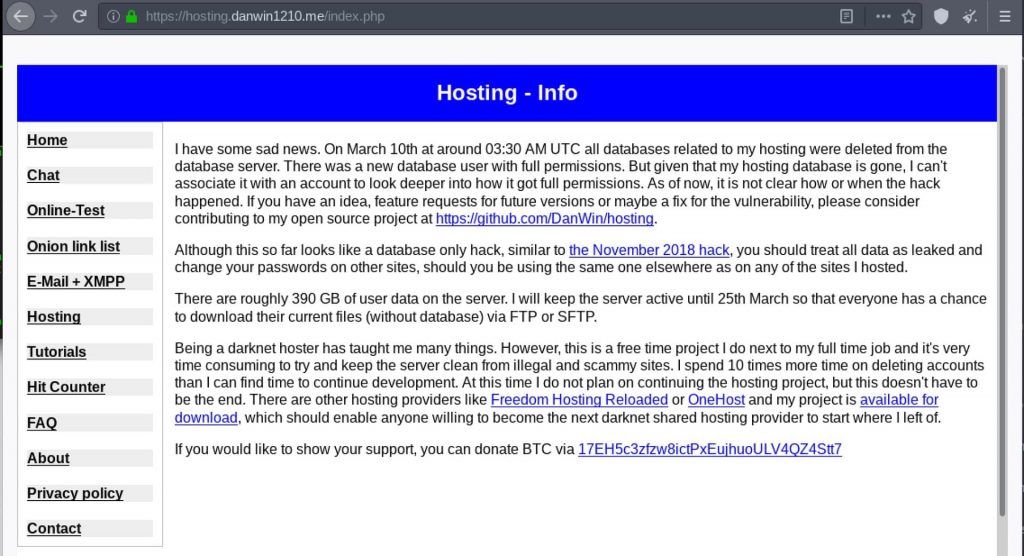
One such free hosting service named Daniel’s Hosting (DH) was run by a German developer named Daniel Winzen with approximately 7600 websites on the dark web. However, a few weeks ago on the 10th of March at 3:30 AM UTC on Tuesday, Daniel released a notice stating that all databases of his hosting service had been deleted which means that the company may not continue operating for the foreseeable future.
Due to security reasons, no backups were available to be restored. This happens to be the second attack in the past 16 months on the service.
Message from the site’s owner:
As Daniel describes that the “hosting database is gone” along with the fact that the attackers set up an entirely new database account, this makes any investigation efforts on who was behind the hack or how it happened futile. The culprits though could be anyone ranging from law enforcement agencies to state-sponsored attackers.
Despite the fact that user accounts in themselves are not believed to have been affected, users were advised to take security precautions and change all authentication credentials as their data may have leaked. Moreover, in line with commitments to his users, the hosting server was still kept active for 2 weeks after the incident so that no one lost their data and could safely download it.
The reason given for not continuing this project is the difficulty Daniel finds in dedicating time for it having a day job. Because the dark web is filled with malicious actors who may be setting up websites hosting illegal content such as drug marketplaces and child pornography, he has to spend time trying to keep his server clean.
However, when DarkOwl – a Darkweb security and intelligence firm – analyzed the 6500 sites lost back in 2018 due to an attack on Daniel’s Hosting, the following results were revealed:
- 657 sites had a title “Site Hosted by Daniel’s Hosting Service” and so the nature of the content present on these sites could not be found,
- 457 sites dealt with hacking and malware development,
- 304 sites consisted of forums,
- 148 sites were chatrooms,
- 136 sites contained keywords involving drugs hinting at illegal activity,
- 109 sites had content involving fake products and services,
- 54 sites had carding related content,
- 20+ sites had content involving weapons and explosives, potentially used by illegal arms traders and terrorists,
- 4900+ of these sites were in English, 54 in Russian and 2 in Portuguese.
This shows that despite Danial’s best efforts in deleting malicious accounts, he wasn’t very successful. For the time being though, his decision to keep the site down isn’t final. As seen in the notice above, he has asked users to contribute if possible by fixing a vulnerability or suggesting a feature for any possible future version.
Nonetheless, being one of the largest hosting websites on the dark web, this represents a blow to the community that values anonymity over the speed and accessibility of the surface web.
Did you enjoy reading this article? Like our page on Facebook and follow us on Twitter.