We come across data breaches exposing sensitive data every day. Some are small in nature, some big enough to be reported in the media. Regardless of the publicity, there are actors out there that use this exposed data to make money through different malicious methods such as ransomware or simply selling the data to interested parties.
One such actor engaging in the latter happens to be a website named WeLeakDatacom. Operating as a forum that helps connect buyers and sellers of stolen and breached databases; it does so through the help of its management who according to research firm Cyble, are well connected to hacking groups and hence have attracted significant publicity.
See: OGUsers hacking forum hacked; entire database dumped on rival forum
Further, it uses Shoppy, an e-commerce platform to manage its membership system ensuring the site functions smoothly. It is worth noting that terabytes of stolen data was also being sold on Shoppy.
However, just recently, a team at Cyble has discovered that the site was breached itself in a chain of events. Firstly, there were rumors in January 2020 that the site had been taken control of by the FBI as it was offline even though these claims could not be substantiated.
Don’t confuse WeLeakData with WeLeakInfo, the latter was seized by the FBI in January 2020.

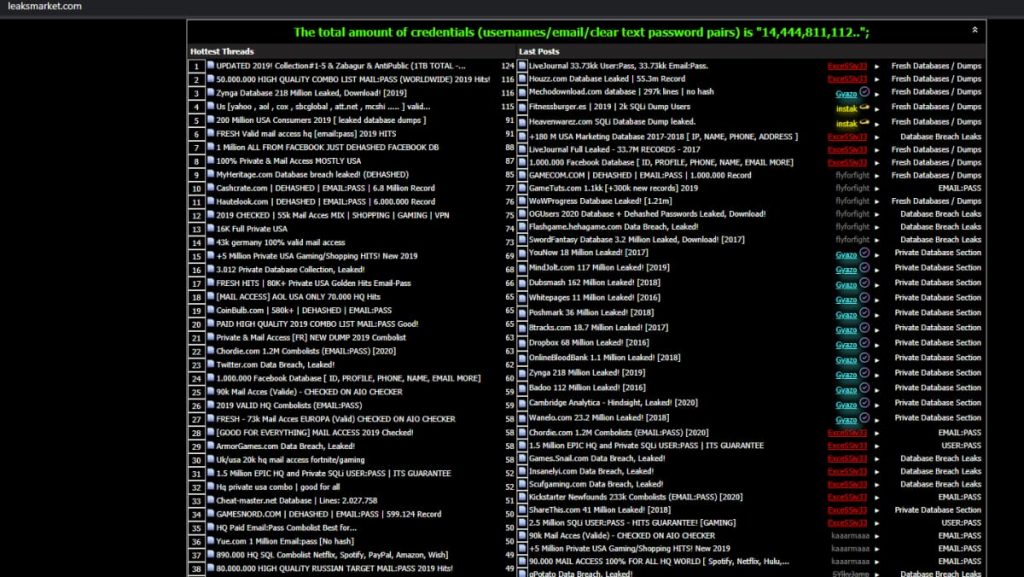
On the other hand, members of WeLeakData also pointed out to the researchers that this was not the case. However, when it did come back online, there were reports that it had been sold to a new member. Yet, at the very same time, a duplicate version of the site also sprang up named leaksmarketcom with the very same exact listings.
In a blog post, Cyble’s researchers wrote that:
It was clear to us by then, the original WeLeakData database has been compromised, or the original owner has decided to re-brand it. However, when they came back online in April, the second hypothesis got nulled, and we then had a high degree of the confidence level of a data breach, at one of the largest cracking communities itself.
Then last month in April 2020, Cyble was able to find the database of WeLeakData on a dark web marketplace confirming their suspicions, the company told Hackread.com.
Contrary to what happens usually, this time the database contained confidential information about the criminals behind the site including their:
- Emails
- Usernames
- Passwords
- Private Messages
- IP addresses
All of these can be used to trace down these criminals and consequently result in criminal prosecutions. However, the use of aliases may make this difficult as most likely these cybercriminals were using VPNs to hide their real IP address. This would require law enforcement agencies to use the other available information and form a picture based on that.
An example of the messages obtained is in the photo below:

Although the code alongside reduces their readability, the messages can be seen nonetheless. Owing to these revelations, it is possible that certain arrests conducted by Europol recently may have included the site’s owner.
See: Over half a million Zoom accounts being sold on hacker forum
To conclude, for the future, we are yet to see a disclosure of the real identity of the site’s owner, although Cyble has debunked their alias. For those of you who may be concerned about your data, you can check if you were a part of WeLeak’s database by entering your email address at amibreached.com.
Did you enjoy reading this article? Do like our page on Facebook and follow us on Twitter.