The FireEye cyber security firm has discovered that a number of Canadian mines and casinos were hacked by a group named FIN10 whose location has not yet been identified – FireEye labels FIN10 to be “one of the most disruptive threat actors observed in the region.”
Sensitive data and information were stolen: As part of the campaign, FIN10 has apparently hacked into the networks of different mining companies and casinos in Canada and has stolen critical information with regards to customers’ habits and other system-level data.
According to the firm’s research (PDF), FIN10 has been on the loose since 2013 and had gone undetected till 2016. It is only now that the attacks have been linked to the group. However, the identity and location of the perpetrators remain to be unknown.
The senior manager of FireEye Charles Prevost unclear why Canada has been the primary target. However, it has been identified that the criminals might be native English speakers.
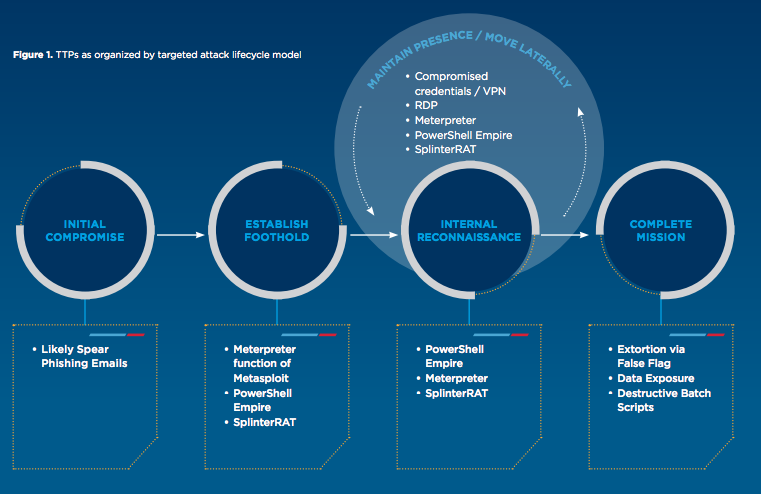
How was the attack carried out? The group has used the conventional ransomware method wherein FIN10 has been able to inject ransomware into the networks belonging to mines and casinos.
FireEye states that the campaign involved the usual method of spam emails in which malicious links, attachments, and documents were contained. The user was tricked into clicking these for the attack to launch itself.
Essentially, once the user clicked one of the links, he/she would be led to a website that would be masked as either a legitimate holiday scheduling system or a document. Clicking or accessing these would activate the ransomware.
Further investigation showed that although the attacks were far-reaching, they were not as high-profile as those launched by Russian hacking groups. In fact, the group used common tools such as PowerShell to infiltrate the system.
Data stolen included information on customer betting habits from casinos and other relevant information belonging to mining companies. Also, the malware allowed the hackers to delete or change files and affect critical databases.
The ransom demanded: The ransom demanded was around 100 to 500 bitcoins, equivalent to 35,000 to 170,000 Canadian dollars, to be paid in 10 days if the victims did not want their data to be released publicly.
Those who did not comply with the group’s terms had their systems completely shut down, closing down all operations altogether.
Victims’ names not yet revealed: When asked about who were the victims, FireEye did not tell the specific names and simply told that less than ten companies have been infected. However, there have been recent attacks that targeted certain casinos including the Cowboy’s Casino along with mining organizations such as the Goldcorp and Detour Gold Corporation.
Although not confirmed, but the same casinos and mining companies might have been the victims of FIN10 also.
DDoS attacks are increasing, calculate the cost and probability of a DDoS attack on your business with this DDoS Downtime Cost Calculator.