The most recent campaign involving the Glupteba Botnet, which started in June 2022, is more extensive than previous ones as it uses over one dozen Bitcoin addresses and involves using Tor services for C&C operations.
Nozomi Networks, an OT and IoT cybersecurity firm, published a blog post revealing that the Glupteba botnet is still active. This negates Google’s claims of disrupting it in a cybercrime operation.
In December 2021, Hackread.com reported that Google had claimed to disrupt the C&C infrastructure of the Glupteba blockchain botnet and also filed a lawsuit against its Russian operators, Dmitry Starovikov and Alexander Filippov. However, according to Nozomi, this botnet is operational.
Campaign Details
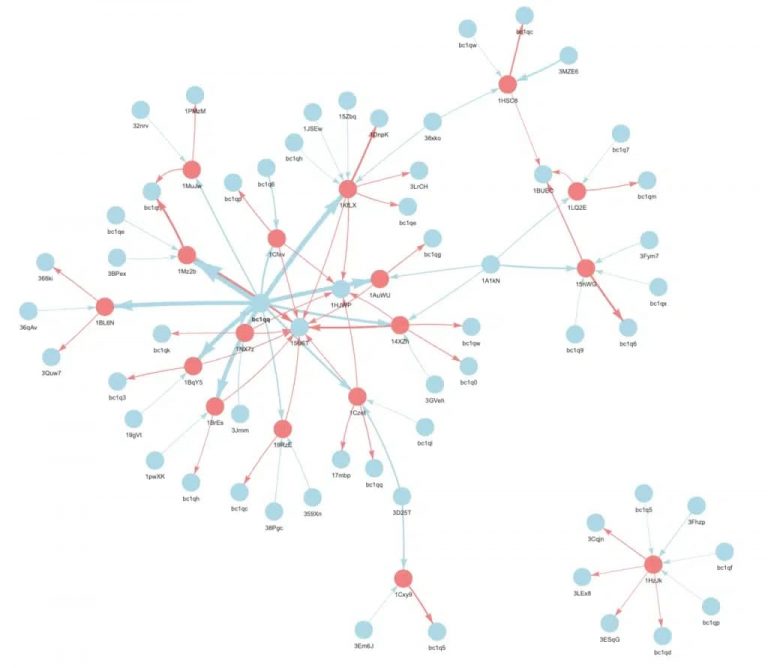
The company noted that the latest campaign involving Glupteba was started in June 2022 and is still ongoing. Researchers evaluated over 1,500 malware samples and scanned an entire Bitcoin blockchain, concluding that the first campaign started in June 2019 using a single Bitcoin address to distribute malicious domains.
Another campaign using the same botnet was discovered, which began in April 2020. This involved using two Bitcoin addresses for C&C domain distribution. The third campaign started in November 2021. It was the shortest campaign as it was stopped only after two months, probably after Google’s intervention.
The most recent campaign, which started in June 2022, is more extensive than previous ones as it uses over one dozen Bitcoin addresses and involves using Tor services for C&C operations.
“In addition, there was a tenfold increase in TOR hidden services being used as C2 servers since the 2021 campaign,” researchers observed.
How Does Glupteba Botnet Work?
The Glupteba botnet leverages crypto blockchains to protect its C&C infrastructure. It is distributed through fake ads or software cracks. It mainly targets Windows devices and can steal sensitive data, including user credentials, mine for cryptocurrencies, and convert IoT devices from Netgear and MicroTik into proxies.
Further, Glupteba can store arbitrary data via an opcode of up to 80 bytes with the signature script. This method helps the botnet stay resilient against disruption efforts since blockchain transactions cannot be erased by defender mechanisms or law enforcement agencies. It is believed that Glupteba uses the same technique that Cerber ransomware has used since 2019.
Why Is Glupteba Hard to Disrupt?
Researchers at Nozomi Networks wrote that since the Bitcoin blockchain is developed using modern cryptography, the mechanism is highly secure so taking over the botnet is impossible. In addition, threat actors can easily encrypt payloads and ensure a cost-effective and robust data storage scheme.
Google claims to have won the lawsuit against Glupteba operators, and the court ordered the defendants and their attorney in the US to pay legal fines. The defendants claim they will cooperate but misled the court as they used the court to obtain information that would help them bypass Google’s attempt to take down Glupteba.
Now the operators have resumed their activities on different non-Google-based platforms and IoT devices. However, the company claims its disruption attempt was partially successful, as it caused up to a 78% reduction in the number of infected hosts.





