Andrew Leonov, a security researcher, discovered a critical remote execution bug on Facebook allowing him to breach the security of social media giant through ImageMagick flaw which was previously reported and patched in 2016 yet Leonov was successful in using the flaw to carry the attack against Facebook servers.
In a blog post, Leonov explained that he reported the issue to Facebook in October 2016 according to which the ImageMagick flaw was still active and impacted Facebook. He also provided Facebook security team with an in-depth proof of concept (PoC) who patched the issue and awarded him a sum of $40,000 through the Bugcrowd payment system.
Must Read: 10 Famous Bug Bounty Hunters of All Time
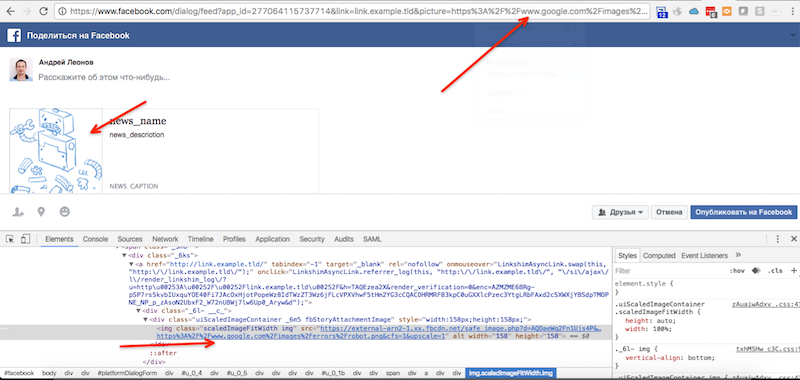
Leonov explained that it all happened unintentionally when he was looking for a flaw in another service which redirected him on Facebook and further digging allowed him to discover the remote execution bug.
“Once upon a time on Saturday in October I was testing some big service (not Facebook) when some redirect followed me on Facebook. It was a «Share on Facebook» dialog. “I am glad to be the one of those who broke the Facebook,” said Leonov.
It must be noted that the largest payment awarded by Facebook as a part of its bug bounty program was $33,500 to Reginaldo Silva back in 2014 who also reported a similar remote code execution bug. To confirm the payment, The Register has contacted Facebook.
Must Read: Hacking Facebook Account by Simply Knowing Account Phone Number
At the time of publishing this article, there was no official statement from Facebook or CrowdBug confirming whether Leonov was awarded $40,000 or not. However, this is not the first time when ImageMagick security flaw is in the news for all the wrong reasons. In 2016, a hacker used the same flaw to destroy Fur Affinity Art Gallery website.





