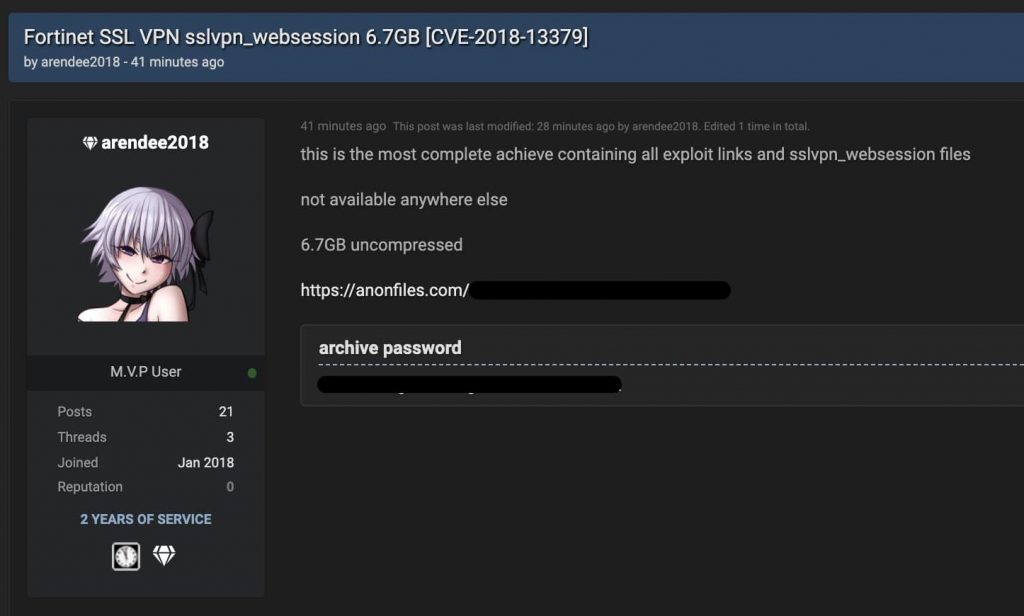
6.7 GB worth of sensitive details citing Fortinet SSL VPNs vulnerability have been leaked on a prominent hacker forum.
On 19 November, a hacker using the alias “pumpedkicks” published a large list of one-line exploits of around 50,000 Fortinet FortiGate IPs containing a path traversal vulnerability classified as CVE-2018-13379.
This vulnerability mainly affected Fortinet’s unpatched FortiOS SSL VPN devices. The exploits could be used for stealing VPN credentials from the internet-reachable VPNs. The hackers also then claimed in a tweet that they possessed the clear text credentials associated with these IP addresses.
Now, in the latest, just 15 hours ago, a researcher has reported an update on the incident showing us that the attacker has revealed those plain-text credentials which are now being shared on other forums as well which allows viewers to not only see the usernames & passwords but also the access levels of those users.
The file posted in itself is a compressed archive worth 36 MB but in actuality is of around 7 GB when opened hinting at the fact that the data would be extremely useful for malicious actors.
It could be used in brute-forcing attacks for the future and would require many users to stop using any compromised passwords even on other sites immediately in order to protect themselves.
The list has been posted on social media and the internet and contains domains owned by high-street banks and government organizations from different parts of the world. Some internet protocol addresses were assigned to domains registered in Australia.
To exploit the path traversal vulnerability, attackers need to remotely download the FortiOS system files, which won’t ask for authentication if the SSL (secure sockets layer) VPN service is activated. This way, attackers can access the sslvpn_websession files easily to obtain login credentials of users who are logged in SSL VPNs.
— Bank Security (@Bank_Security) November 25, 2020
To conclude, Fortinet issued patches for the FortiOS operating system in May 2019. Regardless though, the vulnerability has been exploited again and again thanks to users not upgrading their systems. This therefore naturally places the burden of responsibility on users.
Did you enjoy reading this article? Kindly do like our page on Facebook and follow us on Twitter.