Facebook paid a cybersecurity company to develop a hacking tool exploiting zero-day in Tails OS used by the abuser ultimately leading to his hack, track, and arrest.
Taking an unprecedented step to help the US Federal Bureau of Investigation (FBI) identify and capture a criminal, Facebook played a key role in tracking down Buster Hernandez, a/k/a Brian Kil, a/k/a Purge of Maine, a habitual child predator.
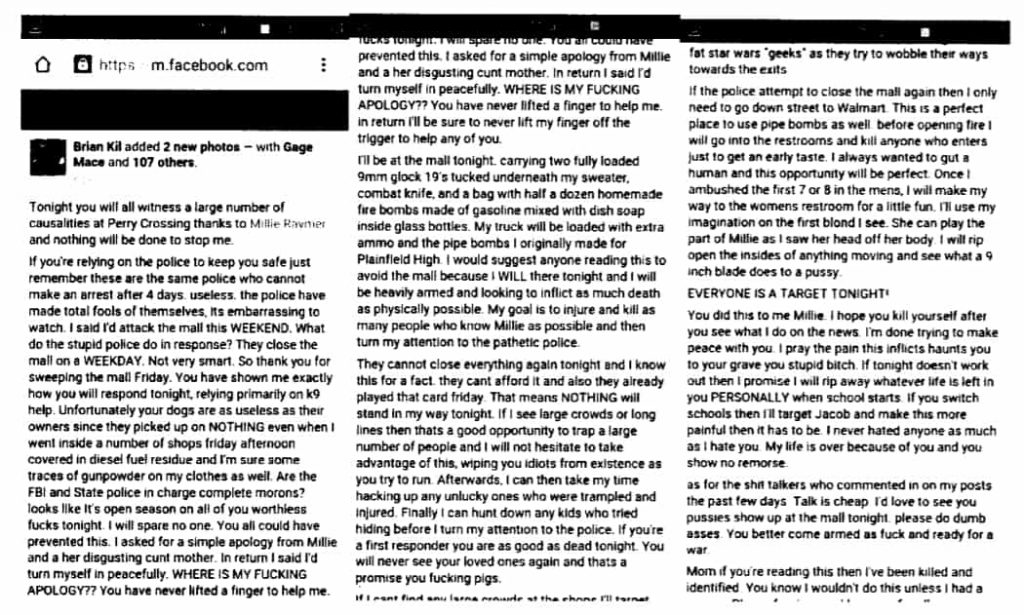
Reportedly, the California resident had been harassing, exploiting, and extorting young girls to send him their nude photos and videos. He not only threatened to rape and kill them but also sent them explicit messages informing that he can carry out mass shooting and bombing at their schools if they don’t fulfill his demands.
See: Dark Web child abuse gang busted; 15TB of files seized
This exploitation was going on for years, and most of the communication was carried out through Facebook, email, and chat apps. Taking a step in the right direction, Facebook decided to cooperate with the FBI to locate the harasser.
The social network giant then collaborated with a third-party cybersecurity firm for the development of a tool to track and arrest Hernandez.
The reason why the FBI had to seek help from Facebook was that Hernandez was a pro at hiding his real identity, and used Tails OS for this purpose. However, according to Vice, Facebook paid the security firm an amount in six figures to develop a tool that could infiltrate Tails OS.
The hacking tool was developed using an inherent vulnerability in Tails’ video player. Using the tool, Facebook was able to obtain the real IP address of the person playing the videos.
Hide your IP address & surf Internet anonymously with IPVanish
The tool was later sent to the FBI via an intermediary source. The bureau took one of the victims on-board to send Hernandez a booby-trapped video. This is how the predator was eventually arrested.
Hernandez has pleaded guilty to all the charges raised against him, most of which are horrific. The court documents are available here.
Although Facebook’s role in capturing the child abuser is admirable, however, the very strategy that the social network adopted violates its privacy policy.
Therefore, is it acceptable that a company gets an exploit created to hack any of its users that too, using an exploit about which Tails’ development team wasn’t informed about? After all, there are countless Tails OS users, and not all are suspected of cybercrime.
See: Dark web’s largest child porn marketplace seized; 338 suspects arrested
A Facebook representative explained that this is the only time the company has helped law enforcement authorities considering the nature of the crime, and it will not be repeated in the future.
“This was a unique case because he was using such sophisticated methods to hide his identity, that we took the extraordinary steps of working with security experts to help the FBI bring him to justice,” the spokesperson added.
In a press release, the Department of Justice is urging other victims of Brain Kil to come forward and contact authorities on tips.fbi.gov or call 317-595-4000.
This however is not the first time when a third-party company has helped the FBI to bust a child predator. In 2017, PureVPN aided the FBI to track cyberstalker by providing his logs to the agency even though PureVPN claimed it does not collect users’ logs.
Did you enjoy reading this article? Do like our page on Facebook and follow us on Twitter.