The Twitter Bitcoin scam allowed hackers to rake in over £80,000/$100,000. Here’s how they got arrested in the US and the UK.
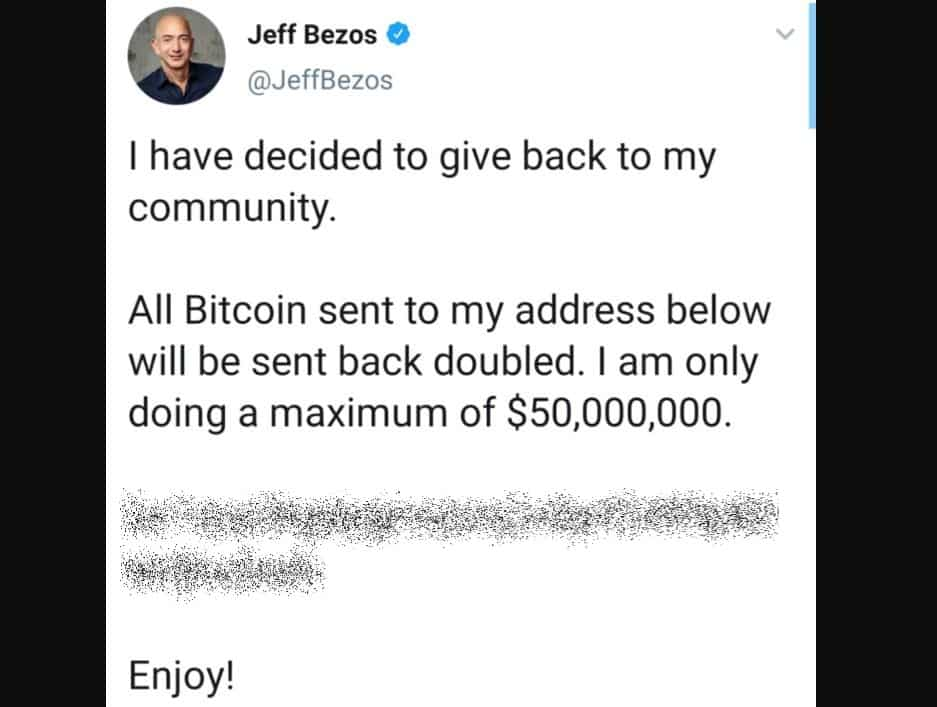
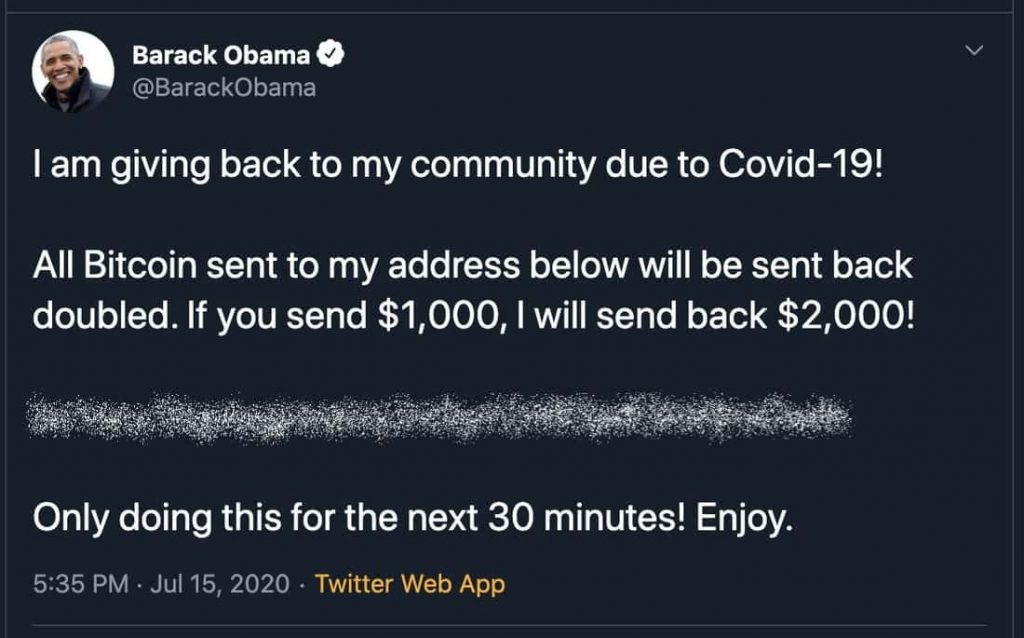
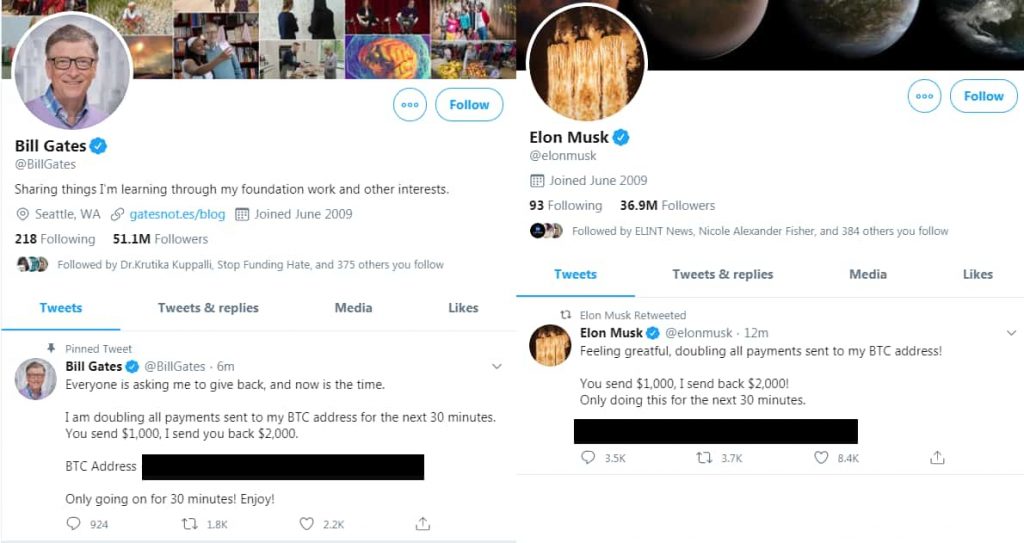
A few weeks ago, we saw about 130 Twitter accounts of several famous people like Elon Musk, Barak Obama, Kim Kardashian, and Bill Gates being hijacked through phone phishing with the attackers asking for Bitcoins in subsequent unauthorized tweets.
The action soon followed with 3 individuals being charged for the hack by the Department of Justice (DOJ) including 1 juvenile. But how did they get caught? Luckily, the DOJ has publicly revealed the court documents which shed light on the entire incident.
To start with, the 3 criminals charged can be identified with their Discord usernames which is essential to understand how the entire scheme worked:
1: 22-year-old Nima Fazeli from Orlando Florida – Rolex#0373
2: 19-year-old Mason John Sheppard from the UK – anxious#001 & Chaewon
3: 17-year-old Graham Ivan Clark from Tampa, Florida – Kirk#5270
In the very beginning, Graham approached both John and Nima on Discord claiming to be working for Twitter as shown in a screenshot below.
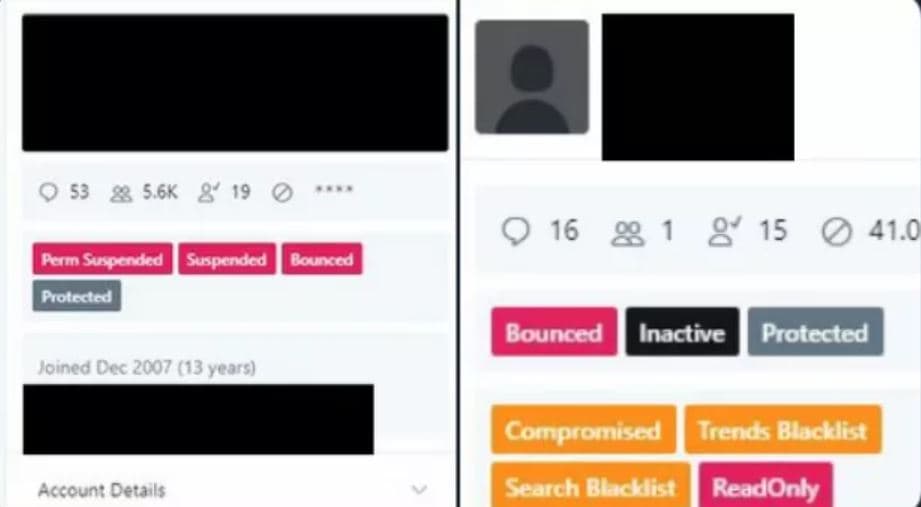
Once they were convinced, the latter 2 helped Graham sell access to different Twitter accounts on underground forums with one example being OGUsers (dot) com, a platform known to host such an illegal market.
However, luckily this very marketplace had been breached earlier in April 2020 and May 2019 which had exposed the email address of Nima letting the FBI learn of this information. Then when they compared this email to the one that Nima had provided to Graham on Discord, it matched!
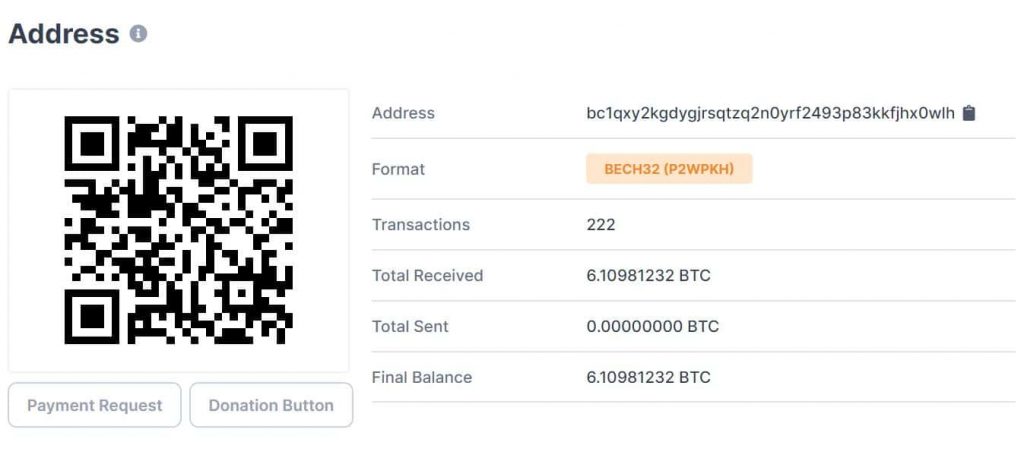
Continue their investigation, the FBI approached Coinbase to know more about a Bitcoin address that Nima had shared on OGUsers and found that it was registered using the same email address that had been used by Nima for registering his account on OGUsers.
Suspiciously, it had engaged in over 1900 transactions which would be worth about 21 Bitcoins or $230,000. Furthermore, due to Coinbases’s Know Your Customer (KYC) requirements, he had also provided them a picture of his driver’s license.
Next, the IP address from which both the Discord and Coinbase accounts were accessed was also found to be the same, originating from Florida. This sealed the Fate for Nima.
Coming to John, he was more or less caught the same way as he too had the same email address being used on Coinbase with his driver’s license also uploaded allowing the FBI to know both his real full name and address. Commenting on this, a special agent of the Washington DC Field Office Cyber Crimes Unit stated,
analyzed the blockchain and de-anonymized bitcoin transactions allowing for the identification of two different hackers. This case serves as a great example of how following the money, international collaboration, and public-private partnerships can work to successfully take down a perceived anonymous criminal enterprise.
As for Graham, it has been reported that he confessed himself being #Kirk5270 after a search warrant was released against him. Moreover, he also stated that he indeed had been responsible for selling Twitter accounts and being in contact with someone from the UK named Mason . More details were not given though on his case if he too was identified through a Coinbase link as the previous 2 suspects.
To conclude, all 3 have severe punishments in place with Graham having his bail set at $725,000; John may face up to 45 years in prison and Nima may face up to 5 years. This incident perhaps will be a big deterrent to the black hat community out there who may have for long gotten the impression that it is easy to get away with cybercrime.
Nonetheless, it is pretty obvious that the attackers too made some rookie mistakes like using the same email addresses on different websites which eventually got them caught.
Did you enjoy reading this article? Do like our page on Facebook and follow us on Twitter.