Researchers from Blue Cat Labs are calling it the Inception attack framework, in reference to the movie “Inception” where a thief entered people’s dreams and stole secrets from their subconscious.
They are also describing it as one of the most sophisticated attacks they have ever seen. That, in itself, is saying a lot for the people at Blue Coat Labs as they have seen it all.
The main reason behind the name is the many layers used in the design of the malware and it launches very highly targeted attacks to enter their victims’ computer and steal confidential information from them.
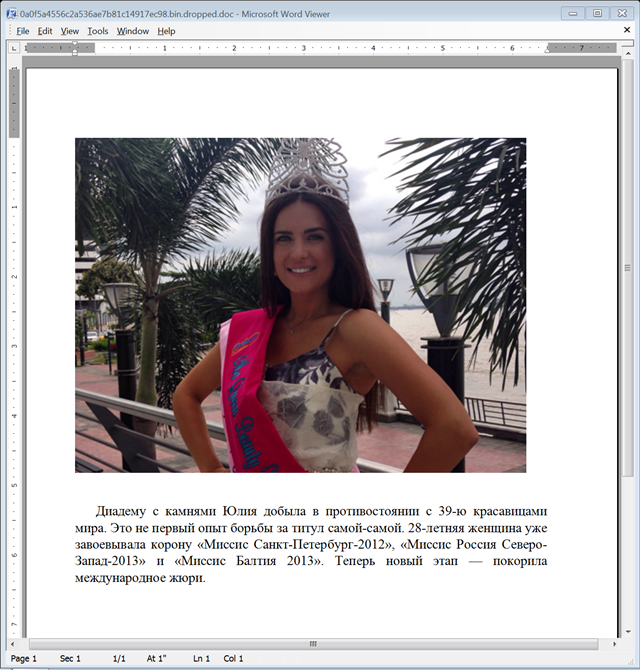
There is yet a lot to be understood about the Inception framework attack as it is currently still enshrouded in mystery. What is clear about the malware is that it attacks through a spear phishing email and also target mobile devices including Android, Blackberry and iOS through planned MMS phishing campigns. Over 60 mobile providers have been hit including China Mobile, O2, Orange, SingTel, T-Mobile and Vodafone. But the senders are yet to be unveiled as they have placed certain clues in the malware that has easily thrown off their scent.
Initial speculations suggest they could be from India as there is Hindi used in some of their Android malware. They may be in the Middle East somewhere as some Arabic text is used in strings of their Blackberry malware. There is also the suggestion that they may be in the United Kingdom due to the string “God_Save_The_Queen” which was also found in their Blackberry malware. If that wasn’t confusing enough for their pursuers, their connections are routed through several home routers that they have hacked. Many of these routers are in South Korea, placing more pins on the global map to follow them around.
Just to make things more interesting and more geographically spread, the framework uses a free cloud hosting service in Sweden for its Command and Control traffic. This in itself serves to hide the identity of the attackers and may confuse quite a few detection mechanisms.
With their identity so deeply masked, their targets are completely the opposite! While the attacks initially targeted Russia and some Eastern European countries at first, it has gone on to expand globally. The victims of these attacks have included political, military, financial and oil industries. Information regarding specific targets are still not public but Blue Coat Labs researchers have confirmed several phishing emails that targeted the following industries: finance in Russia, oil industry in Romania, Venezuela and Mozambique, and embassies or diplomacies in Paraguay, Romania and Turkey.
Researchers have also unveiled that decoy documents obtained by Blue Coat Labs hint at an interest in the sectors of embassies, politics, finance, military, and engineering.
The initial discovery of the Inception framework came in March 2014 when Microsoft published information about a new vulnerability in Rich Text Format (RTF) named CVE-2014-1761 in addition to two previous RTF vulnerabilities.
The masterminds behind Inception were quick to capitalize on these vulnerabilities at first through phishing emails disguised as real news stories which infect the targets and then, undetected, send the victim’s files back to the Command and Control servers at a Swedish cloud service known as CloudMe, used as the backbone of this whole visible infrastructure. After that, having established a connection with a cloud account, the malware then starts to check subfolders for updates which it then downloads, decrypts and uses.
Naturally, Blue Coat informed CloudMe about this abuse of their services and the Swedish establishment was very quick to help, providing all sorts of log information.
On computers, Inception collects computer name, user name, user group membership, the process it is running in, local ID’s, and system drive and volume information.
With the mobile phone malware, it is similar since the infected phone is used to record phone conversations, to collect location data, contacts and account data. Victims of the MMS phishing attacks can be monitored through their phone calls and their daily texts or activities and wanderings. There seems to be cause to believe that the attacks on mobile phones were aimed at selected individuals and phishing campaigns have been prepares for several countries in Asia, Africa, Middle East and Europe.
Blue Coat Labs describe the malware as having a clean and elegant code which shows quite a strong backing and what they term as top-tier talent, suggesting a very well-resourced and professional organization behind Inception. In other words, it is not the work of a handful of people. The number of layers used to protect the attackers is so advanced that it is even seen as somewhat paranoid.
Since there are very little clues to follow up on, the nature of the targets that are connected with political, economic, and military sectors, seem to indicate that whoever is behind Inception could possibly be a nation state or even a private entity with specific interests.
Blue Coat offers guidance to avoid infection by advising is to keep software updated and avoid jail breaking phones or installing apps from unknown sources. Signs of being targeted include unsolicited emails that contain RTF documents or even MMS messages suggesting that certain phone applications need updating,
Blue Coat Labs seem to think that this is a huge campaign and we have barely seen the beginning of it. The attacks may have started in Russia but it is now clear that there are verified targets all over the world.
Source: Blue Coat.