
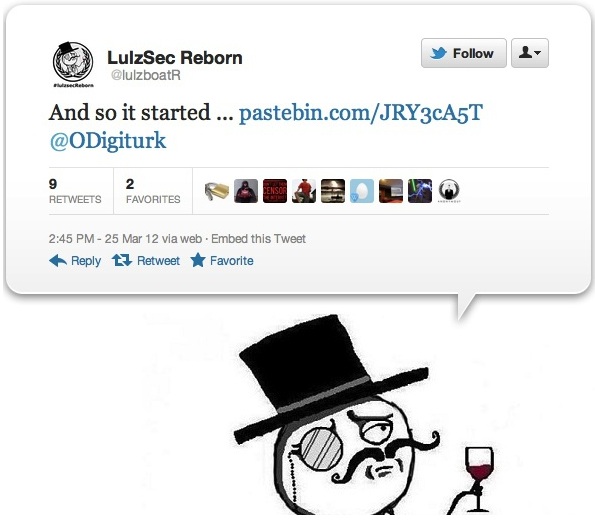
LulzSec hacking crew is back online with hacking into US Military dating website and leaking over 170,000 emails of users online. LulzSec group that was busted last month by their own leader Sabu claims that it is back with a new leader and new plans.
According to the announcement made by the group on pastebin:
“There are emails such as @us.army.mil ; @carney.navy.mil ; @greatlakes.cnet.navy.mil ; @microsoft.com ; etc..,” along with the links for downloading the leaked data.
According to the pastebin message:
The website / was recently closed day ago or so, so we dumped email db
There are emails such as @us.army.mil ; @carney.navy.mil ; @greatlakes.cnet.navy.mil ; @microsoft.com ; etc..
Total Dump 170937 Accounts.
Download Links:
- http://www.embedupload.com/?d=4DR1M2FVGT
- http://www.mirrorcreator.com/files/OOFIKKI6/military.rar_links
“Regardless of whether it was a true or false claim, we are treating it as though it is true just to be safe,” Robert Goebel told the LA Times. He added that the website has a total of 140,000 accounts against almost 171,000 claimed by the hackers. There are doubts the attack took place at all, According to RT.
Meanwhile according to a LulzSec follower ”This is Just another CIA op pretending to be a threat to justify the US Gov in taking over the Internet. “False Flag Attacks” have been working for them since 9/11, so why stop now? Beware of Anonymous and all the other so-called rebel hacker groups, they are all traps; totally infiltrated and mostly controlled. You have been warned”.
At the same time, the group has reported a successful hack of the CSS Corp., a private global information and communications technology company financially backed by several private equity groups, including Goldman Sachs. LulzSec claims to have dumped the whole company’s database, including email addresses, names, usernames, passwords, and IDs. They posted part of the data to Pastebin with a link to download the rest.
