For cybercriminals developing an Android malware is a piece of cake and the problem is Google just not care.
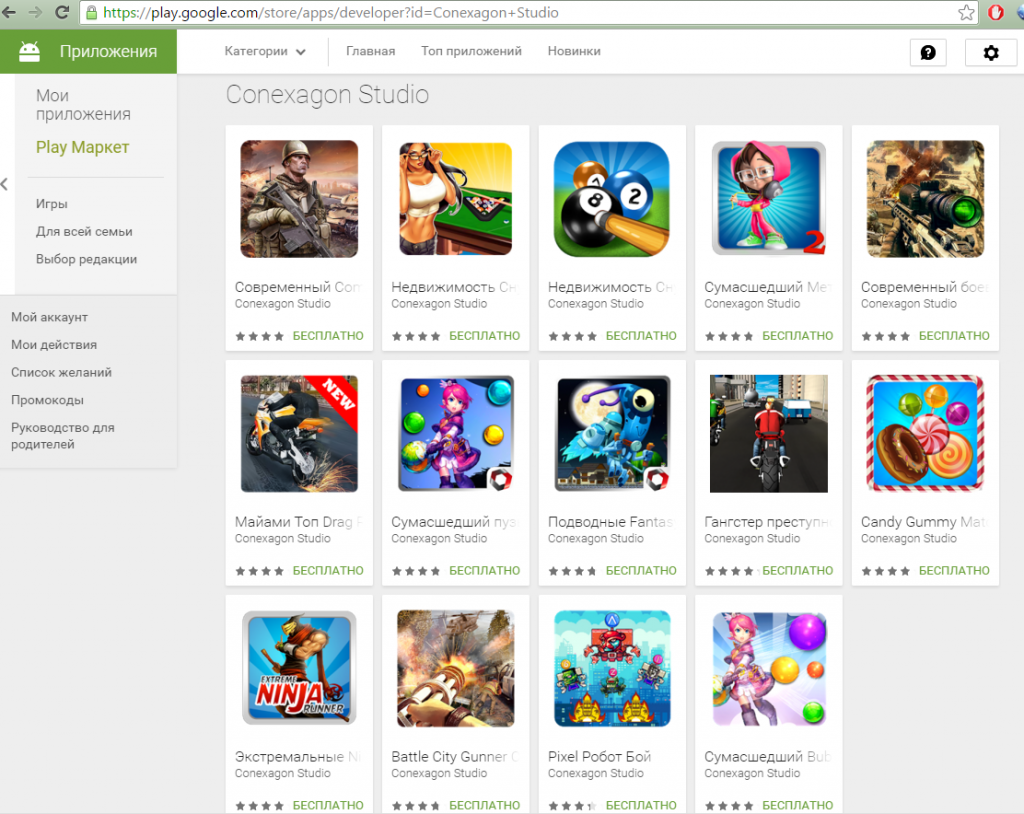
According to Dr.Web’s security researchers, Google’s official Play Store is extremely unreliable because over 60 Android games available on this platform contain Android.Xiny, a malicious Trojan. It was also discovered that around 30 different developers were responsible for uploading these 60+ infected games. However, all the games were so similar in packaging and behavior that these appeared to be uploaded by the same source.

When any of these games were downloaded by users, it resulted in compromising of their personal information, which was then transferred to a remote command and control server. The information collected includes IMEI and IMSI identifiers, mobile operator information, country and language settings, OS version, MAC address of the phone, kind of memory card inserted into the device and the app from where the Trojan was getting all the information.

It makes sense that the Trojan collects information about the app because it happens when the system is infected with multiple malicious apps. This also highlights another fact that these games could have been developed and deployed on the Play Store by the same bad actor.
The malicious Android.Xiny malware displays ads and also invites other malicious apps on the system after installing itself.
When the data is transferred to the related command and control server, according to the phone specifications of the victim, the malware operator instructs the Trojan to escalate its presence in the device by getting other malicious applications deployed on the system along with displaying ads.
However, this malware doesn’t obtain root privileges yet, it can download and takeoff other applications into execution. It contains such powerful code that is enough to root the device and help the attacker gain more control on the device/system/phone.
Dr.Web’s researchers noticed a strange occurring while investigating this campaign, which was the use of steganography for deploying malicious applications.
Steganography involves hiding data that is easily viewable such as images. The operators of Android.Xiny packed other Android apps inside a PNG image and did not choose to hide its download through HTTPS traffic.
This was done so because not many security researchers conducting reverse engineering would feel suspicious about downloading an image as their focus is usually on observing and attempting to track HTTPS traffic since it is a common avenue for malware distribution.
As of now, Google hasn’t managed to take down these malicious apps infected with Android.Xiny malware.




