Recently, Noam Rotem and Ran Locar, analysts at vpnMentor have discovered a data breach that exposed the user data of Conor Solutions, a South African mobile technology company.
This gave the public access to “daily logs of user activity by customers of ISPs using web filtering software built by Conor” exposing their internet traffic in the process as well.
See: 2.7 billion email addresses & plain-text passwords exposed online
Naturally, this included sensitive information including one’s browsing history. The latter ended up embarrassing a lot of users. Moreover, the company boasts over 80 million users of its products and notable clients such as Vodafone increasing the severity of the breach.
According to the official report released by vpnMentor, they first discovered the company’s database on 12 November. What makes this incident come to our notice now can be attributed to the lack of identification associated with the database once it was discovered.
Soon, however, a connection was discovered to a web filter app built by Conor and thereby they were informed of the issue.
As common with data breaches, this particular database was also unencrypted and without any authentication measures in place. This makes us question how oblivious the cybersecurity team of such a large firm can be.
See: This Smartwatch is exposing real-time location data of thousands of kids
It’s worth mentioning that vpnMentor themselves had access to user activity logs numbering over 1 million records for the past 2 months which were being continually updated equating to over 890 GB of data. These as mentioned earlier were users of various ISPs based in “African and South American countries.” Explaining further, they stated,
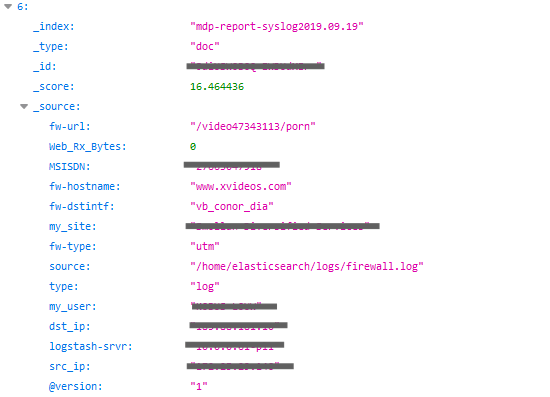
“The software seemed to be a Web filter developed for ISP clients to restrict access to certain websites and types of online content. We found entries from users viewing porn for example, as well as their social media accounts.”
The personal data obtained has also been highlighted as shown in the image below. It contains critical fields such as the IP address of users. Furthermore, each user could be personally identified making it a nightmare for users. For example, if an attacker had exported those records, they could potentially trace and blackmail you.
But this is not all since the database contains highly confidential info, it also gave an insight into how Conor’s web filter works allowing anyone to learn how to bypass it. Hence, in the near future, not only will Conor have to work on repairing user trust but also fixing the loopholes that it has revealed in its own application.
The complete list of data exposed in the breach is as follow:
- The index names: allowing easy identification of daily activity
- MSISDN: a code that identifies a mobile phone user within their provider’s network, via their phone number
- IP address
- Duration of connection or visit to a website
- The volume of data (in bytes) transferred per session
- Full website URL
- If a website had been blocked by the filter or not
Did you enjoy reading this article? Like our page on Facebook and follow us on Twitter.





