Search Results
Microsoft
1156 posts
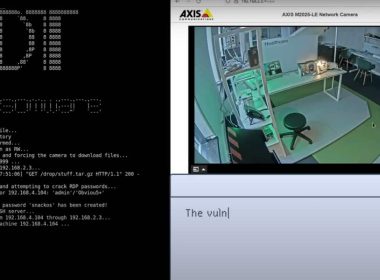
New PoC Shows IoT Devices Can Be Hacked to Install Ransomware on OT Networks
In this PoC, the ransomware attack dubbed R4IoT uses vulnerable IoT devices (in this case, vulnerable security cameras)…
June 1, 2022
How To Screencast on Windows 10
Screen recorder for Windows is a useful feature that comes in handy for a variety of tasks, especially…
May 27, 2022
5 Casual Games You Can Play on Your Mobile Browser Now
Online gaming has always been the buddy of leisure time because they allow us to bring some enjoyment to…
May 21, 2022
Beware of Fake Windows 11 Downloads Distributing Vidar Malware
Phishing domains are spreading Windows 11 installers loaded with Vidar infostealer. According to the cybersecurity firm Zscaler ThreatLabz, threat…
May 20, 2022
Secure Email Gateway Vs. Integrated Cloud Email Security (SEG Vs. ICES) – What’s the difference, and which should my business use?
When you think of phishing or any form of internet crime, many believe this is something completely remote…
May 16, 2022
USB-based Wormable Raspberry Robin Malware Targeting Windows Installer
The malware Raspberry Robin is distributed via external drives and uses a Microsoft Standard installer to execute malicious…
May 6, 2022
DDoS Attacks by Hacktivists Disrupted Russian Alcohol Supply Chain
Attackers from the Ukrainian IT army successfully disrupted alcohol shipments in Russia by targeting EGAIS, the country’s primary…
May 6, 2022
How to detect phishing images in emails
Phishing has long been a common way to induce a receiver to unveil personal data. Primarily, it works…
April 27, 2022
Ransomware Attacks: Everything You Need to Know
Learn everything there is to know about ransomware attacks. We cover the definition, statistics, and ransomware protection. Even…
April 26, 2022
Lapsus$ Hackers Stole T-Mobile’s Source Code and Systems Data
T-Mobile has acknowledged the breach which occurred before police arrested some of the Lapsus$ members last month. The…
April 25, 2022