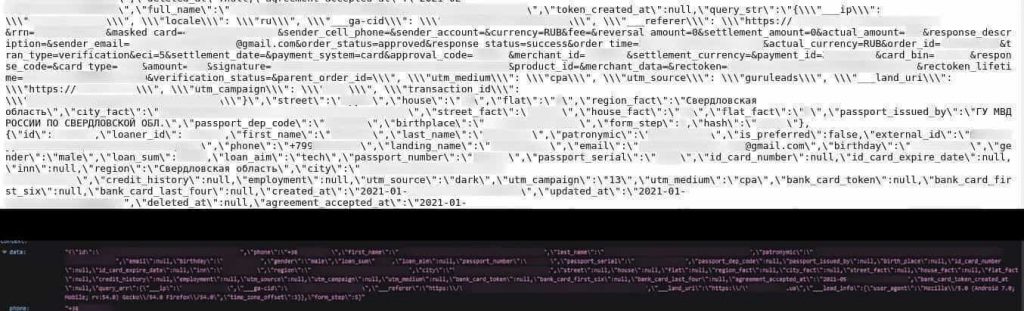
The trove of data was leaked due to a misconfigured Elasticsearch server and in total it stored 870 million records or 147 GB of data.
SafetyDetectives security team led by Anurag Sen shared details of a misconfigured Elasticsearch server that exposed the data of millions of loan applicants. The data mainly belonged to people from Ukraine, Kazakhstan, and Russia who had applied for microloans.
The server was detected randomly on December 5th, 2021, while checking certain IPs however the details of it have only been shared this week. The anonymous server was left unsecured and unprotected as it didn’t have any authentication protocols, which led to the leaking of more than 870 million records or 147GB of data.
Owner Identity Yet Not Available
SafetyDetectives couldn’t determine who owned the server. However, researchers noted that customer logs of numerous microloans providers’ websites were stored on the server, but most weren’t financial services like lenders or banks. Instead, these websites were of third parties that are intermediaries between the loan company and the applicant.
Most entries in the server’s logs were in the Russian language, while most data belonged to Russians. Therefore, researchers concluded that the server’s owner is a Russian entity.
Details of Exposed Data
According to SafetyDetectives researchers, different forms of personally identifiable information (PII) and sensitive user data got exposed in this leak, including details of users’ “internal passports” and other forms of data.
It is worth noting that In Russia and Ukraine, internal passports are used as the substitute for national IDs and are used within the country’s territories. According to SafetyDetectives’s blog post, the internal passport details contained in the exposed server include the following information of users:
- Gender
- Marital status
- Date and place of birth
- The physical address, including city and region
- Full name with first name, last name, and patronymic name
- Passport number with issue/expiry dates and serial number
Some of the exposed data, such as cities, names, addresses, and issued by locations, were written in Cyrillic script, which is primarily used in some parts of Asia and Europe.
In some instances, this information was decoded into certain symbols. Other PII details exposed by the unsecured server include the following:
- Salary
- Child count
- Loan details
- Mobile numbers
- Email addresses
- Employment status
- Education information
- Login OTP SMS codes
- INN (tax identification numbers)
How Many Users Impacted?
Around 10 million users are expected to be affected by this exposure. Many server logs and passport numbers belonged to Russians, while most INNs belonged to Ukrainians. The server was located in Amsterdam, the Netherlands.
SafetyDetectives contacted the Russian CERT on December 14th, 2021, and the Dutch CERT on December 30th, 2021. However, both refused to help. The server’s hosting firm was contacted on January 13th, 2022, which secured the server the same day.
Potential Dangers
Considering the extent and nature of exposed data, the incident can have far-reaching implications. Such as bad actors can download the data and carry out identity theft, phishing scams, scam marketing campaigns, and microloans identity fraud.
More Elasticsearch database Mess Ups
- 9,517 unsecured databases identified with 10 billion records globally
- New malware attack turns Elasticsearch databases into DDoS botnet
- Stripchat database mess up exposes 200M adult cam models, users’ data
- US and China Exposed Most Databases Among 308,000 Discovered in 2021
- Misconfigured ElasticSearch Servers Exposed 579GB of Users’ Website Activity