Copyfish extension of Google Chrome lets users extract textual content from PDF files, images, and videos. It is a widely used extension having over 37,500 users. Reportedly, this particular extension has been hacked by phishing specialists after they managed to compromise the account of German developer team a9t9 at Chrome Web Store.

Now they are using this extension for distribution of spam messages for trapping innocent users. The perpetrators of this attack are yet unknown, but it is clear that they have inserted advertisement injection capabilities in the extension.
A9t9 software stated that the hacking suspicion emerged when a member of the team received a phishing email that looked just like the one usually sent by Chrome Web Store’s team. It stated that the recipient must update their Copyfish Chrome extension or else Google will be removing it from its Web Store.
The recipient was asked to select the “Click here to read more details” button that opens a Google password dialog box. The password is to be entered at a bit.ly link. The recipient, a member of a9t9 software, was viewing the email in HTML format. Therefore, he did not receive any warning message and continued to enter the password from his developer account.
It was identified that hackers had replicated the password screen immaculately as it looked the same as on Google. At this point, the developer team had not suspected phish attack because “Chrome extension was simply not on radar screen.”

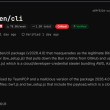
After the team member entered credentials of a9t9 software’s developer account the Copyfish extension was updated to the hacker’s version, which was version 2.8.5. This version is sending spam messages and ads to its users.
It must be noted that only the Chrome version of Copyfish is hacked whereas its Firefox version is safe. The attackers prevented the developers of extension from eliminating the infection by moving the extension. This is why Copyfish developers still have no control over it, and they suspect that the hackers may update the extension later. It is identified that the hack attack occurred on 28th July.
Developers issued an official statement as well, which read: “So far, the update looks like standard adware hack, but, as we still have no control over Copyfish. We cannot even disable it—as it is no longer in our developer account.”
Google has been contacted and notified by a9t9, and the tech giant is already working on ensuring that the company can access its software. A9t9 software also urged users to stop installing any version of Copyfish for the time being and delete it if they have installed.
At the time of publishing this article, the Copyfish extension was deleted from Chrome web store.