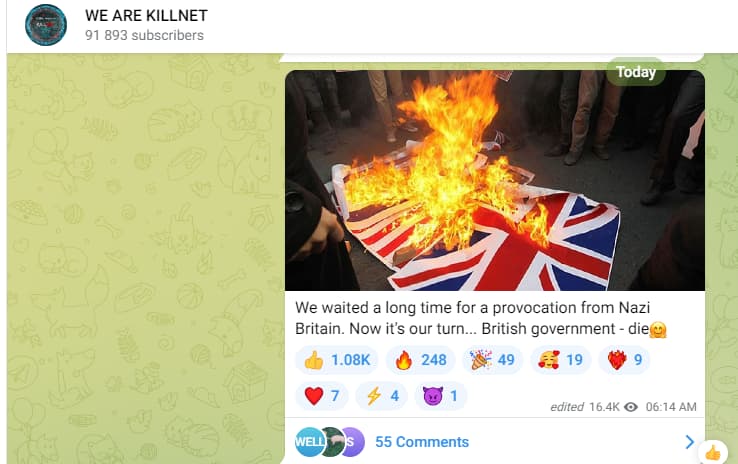
On November 22nd, in the early hours of the morning, Prince William’s website was reportedly attacked by a Russian hacking group Killnet. In a message posted on Telegram, Killnet stated the reason for the attack to be UK’s continued support for Ukraine.
Killnet said it had conducted the attack “due to the supply of high-precision missiles to Ukraine.”
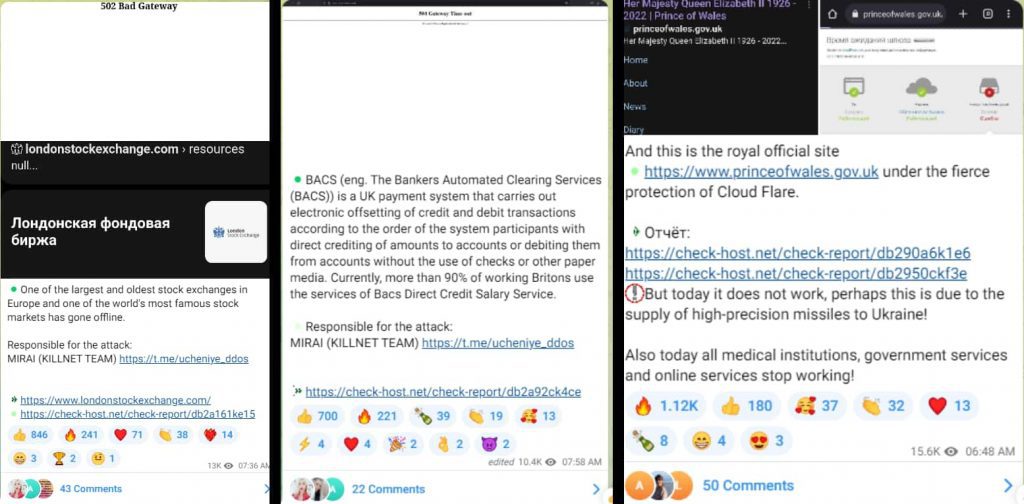
Although the website is now functioning, there are additional security checks on the connection by Cloudflare (the company that provides secure web connections) which were not present before.
The attack appeared to be a distributed denial-of-service attack (DDoS attack) which causes a server to be overwhelmed by numerous bogus requests, usually from bot servers – something Killnet is well known for. However, this information has not been confirmed.
Killnet also declared in a message on Telegram that “all medical institutions, Government services, and online services” could soon be attacked as well. In further posts, the group said it was targeting the websites of the London Stock Exchange, the British Army, and the Bankers’ Automated Clearing System (Bacs).
Currently, all three websites are functional however, the British Army website displayed undergoing “planned maintenance” message on Tuesday, November 22nd.
In a conversation with Hackread.com, Muhammad Yahya Patel, Security Evangelist at Check Point Software said “Killnet is a prolific political pro-Russian hacking group that moves targets every few weeks based on geopolitical developments.
As a major player in the hacktivism space, they also suggest and define the targets for other pro-Russian groups. We have seen a 42% global increase in cyberattacks since the start of the Russia-Ukraine war, with a significant rise in state-sponsored groups. These DDoS attacks are the latest efforts from hacktivists to disrupt high-profile websites, including those of the Royal household, as part of their political agenda.”
DDoS attacks are unlikely to compromise data or systems because they simply flood the web server with too many requests so that it cannot respond in time. During the attack, the loss of connection is likely to be short-lived since web operators can identify numerous IP connections originating from the same block.
Therefore, threat actors employing this technique are unlikely to achieve any real damage because this technique is not very successful these days and most companies nowadays employ technologies to offset such attacks.
This is not the first time Killnet has taken it upon itself to wage a cyber war due to the ongoing political situation between Ukraine and Russia. Previously, they tried to take down the Eurovision Song Contest. Due to not being invited, they tried to cause chaos in Italy (the host nation) but were thwarted and Ukraine went on to win the competition.
The group also attempted to take down the online voting servers throughout the final but was unable to break through the “wide range of security measures” that Eurovision officials promised. Instead, they chose to attack several Italian institutions in the semi-final and final in Turin.
RELATED NEWS
- 34 Russian Hacking Groups Stole 50 Million User Passwords
- New DDoS Malware ‘Chaos’ Hits Linux and Windows Devices
- RapperBot malware targets gaming servers with DDoS attacks
- Anti-Russian OldGremlin Ransomware Gang Launches Linux Malware
- DDoS App Meant to Hit Russia Infected Phones of Ukrainian Activists






