Search Results
Cyber Criminals
1603 posts
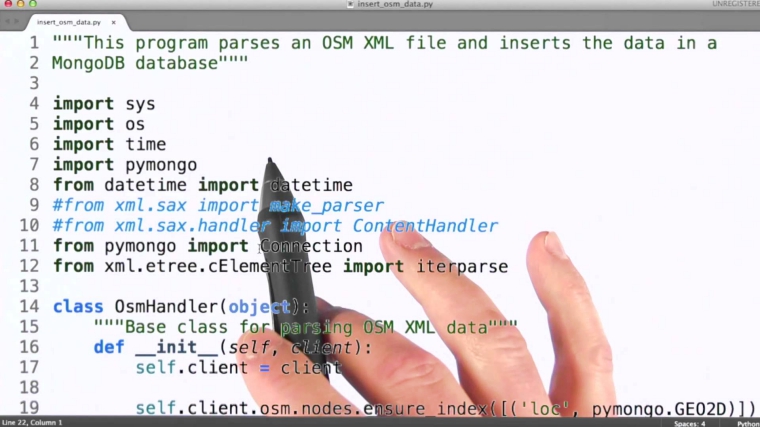
MongoDB Databases being Targeted by Cyber-criminals for Ransom
MongoDB is a famous, open-source NoSQL database. Organizations use them regardless of their size; from MetLife, LinkedIn, City…
January 5, 2017
Cybercriminals Hack Hospital PCs Demand Whopping 9000 BTC Ransom
Ransomware Infects Hollywood HealthCare Facility Computers – Attackers Demand $3.6M Computers are an integral part of almost every…
February 17, 2016
Cybercriminals Can Drop Malware On Your PC Using Video Ads
Visual ads directing users to malicious sites are things of past, cyber-criminals have added a new dimension to…
November 20, 2015
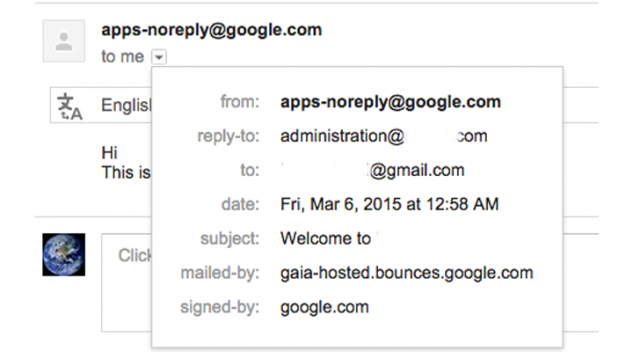
Cybercriminals Abusing Vulnerability in Google Apps to Send Phishing Emails
It has been found that hackers can now easily abuse any website’s domain name based email addresses through…
March 12, 2015
IT and Cybersecurity Jobs in the Age of Emerging AI Technologies
Fear AI taking your IT or cybersecurity job? Don't! Learn how AI creates new opportunities in network management, threat detection & more.
April 19, 2024
Top 3 Cybersecurity Tools to Protect Business Data
Discover the top three cybersecurity tools designed to safeguard your business data from online threats and breaches, ensuring secure data transfer.
April 2, 2024
NHS Dumfries and Galloway Faces Cyberattack, Patient Data at Risk
Another day, another healthcare-related cyber attack putting already vulnerable individuals at risk.
March 19, 2024
ThreatHunter.ai Halts 100s of Attacks: Battling Ransomware & Nation-State Cyber Threats
Brea, California, February 26th, 2024, Cyberwire – The current large surge in cyber threats has left many organizations…
February 26, 2024
Beyond the Charts -The Human Factor in Cybersecurity and Financial Decisions
Beneath the surface of those analytical gear lies a crucial element that regularly shapes the future of investments…
February 13, 2024
Synthetic Solutions: Redefining Cybersecurity Through Data Generation in the Face of Hacking
Cybersecurity is a constant battleground where hackers continuously devise new strategies to breach defences, jeopardizing sensitive information and…
February 5, 2024