The company in the discussion is German shopping giant Windeln.de who did not secure its database despite being alerted by researchers.
A couple of days ago it was reported that a misconfigured Elasticsearch database exposed 882 GB worth of data from 70 dating and e-commerce sites. Now, in the latest database mess up the personal data of more than half a million people has been exposed online.
The team of IT security researchers at Safety Detectives led by Anurag Sen has discovered a database belonging to a German online shopping website “windeln.de” exposing a humongous amount of personal data putting children and parents at all sorts of offline and online risks.
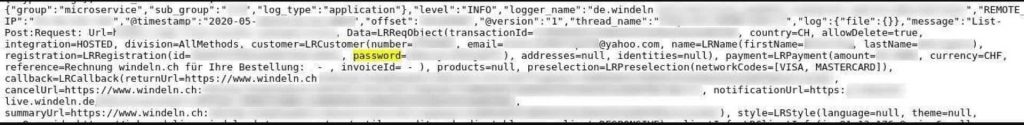
Since Windeln offers products related to miners, it already makes the company a sensitive platform requiring utmost security. However, in this case, the store’s production server database exposed 6.4 terabytes of data containing 6 billion records leaking personal information of over 700,000 customers.
See: Personal details of 38 million+ US citizens leaked in database mess up
It is worth noting that the production database was hosted on the Elasticserch server exposed on Shodan without any security authentication. This means the trove of data was accessible to the public including malicious threat actors and state-sponsored hackers.
As for Windeln, the information exposed in the incident included Personally identifiable information (PII) and other data such as:
Invoices
Full names
IP addresses
Internal logs
Phone numbers
Email addresses
Home addresses
Hashed passwords
Payment methods without payment data
Users’ children data such as their names, dates of birth, and gender.
A full list of exposed data is available on the Safety Detectives’ blog post.
The incident should not come as a surprise since Elasticsearch servers have a long history of exposing data online. Furthermore, misconfigured databases have exposed billions of sensitive records in the last couple of years.

Information relating to children is particularly sensitive because malicious hackers can exploit the strong bond between parent and child, by, for example, using the child’s birthday as an opportunity to deploy scams upon the parents, warned Safety Detectives.
Safety Detectives detected the breach on June 13th, 2020, and estimate that the database was left exposed for more than a month. What’s worse is that no one from Windeln responded when researchers alerted the company of the breach.
The good news is that the database was secured after researchers alerted German CERT (Computer emergency response team).
Although t is unclear whether the database was accessed by malicious threat actors or not, Hackread.com warns Windeln customers that they must remain alert as they could be at risk of targeted phishing attacks.
Remember, criminals could use the information and pose as Windeln.de’s representatives to conduct fraud. Therefore, any suspicious emails or messages should be ignored by Windeln customers. Also, they must not click on any URL links without verifying the legitimacy of the sender.
Did you enjoy reading this article? Do like our page on Facebook and follow us on Twitter.