Browsing Tag
IoT
314 posts
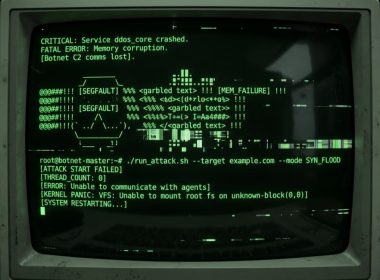
New Mirai Variant Nexcorium Hijacks DVR Devices for DDoS Attacks
Cybersecurity researchers at Fortinet have discovered Nexcorium, a new Mirai-based malware targeting TBK DVR systems to turn them into a botnet for DDoS attacks.
April 17, 2026
13.5M Device Botnet Drives 2 Tbps DDoS Attacks on FinTech, Qrator Finds
A new Qrator Labs report reveals that the largest DDoS botnet has grown to 13.5 million devices, and…
April 15, 2026
wolfSSL Vulnerability Hits IoT, Routers and Military Systems, Update to 5.9.1 Now
Critical wolfSSL flaw CVE-2026-5194 allows digital ID forgery across billions of devices, update to version 5.9.1 to fix the issue and reduce risk.
April 14, 2026
Mirai Malware Evolves into Hundreds of Variants Driving Botnet Growth
Mirai malware evolves into hundreds of variants, driving botnet growth, including Aisuru and KimWolf, powering large-scale attacks, and increasing risks to vulnerable IoT devices worldwide.
March 25, 2026
Global Crackdown Dismantles 4 Botnets Behind Major DDoS Attacks
Global crackdown dismantles Aisuru, KimWolf, JackSkid and Mossad botnets behind major DDoS attack campaigns targeting millions of devices worldwide.
March 23, 2026
Feds Takes Down SocksEscort Proxy Network Used in Global Fraud Schemes
European and US agencies dismantled the SocksEscort proxy network built on infected routers and used by cybercriminals in global fraud schemes.
March 12, 2026
Maintaining Security and Protecting Smart Home Devices from Hackers
Learn how to protect smart home devices from hackers. Strong passwords, updates and secure networks help keep cameras, sensors and data safe.
March 12, 2026
Car Tyre Sensors Can Be Used to Track Drivers Without Their Knowledge
New research from IMDEA Networks reveals how unencrypted signals from tyre pressure sensors in brands like Toyota and Mercedes can be used for covert vehicle tracking. Learn how these low-cost systems can map out your daily routines and why current regulations fail to protect driver privacy.
March 4, 2026
5 IoT Vulnerabilities That Stop Projects and How to Avoid Them
Stop the 75% failure rate. Learn which device vulnerabilities stall deployments and the exact fixes that get IoT projects to production.
February 28, 2026
How to Maximize DDoS Readiness with Proactive Protection Strategies
Strengthen DDoS Readiness with proactive protection strategies, risk assessments, traffic monitoring, scalable defenses, and rapid response planning.
February 24, 2026