The vulnerability affected Telegram’s desktop app for Windows, Mac, and Linux OS.
Telegram, a popular privacy-focused instant messaging application, reportedly contained a bug that can leak the IP addresses of users. Known for providing end-to-end encryption, Telegram’s desktop app has been discovered to be leaking not just public but private IP addresses of its users by-default during voice calls and users cannot turn off the feature.
This means, anyone and everyone attempting to make a voice call will be vulnerable to cyber-attacks. Telegram has, however, fixed the bug in one of the latest updates and the security researcher who identified the bug has been awarded EUR 2,000 by the company.
See: Snowden Explains Why Telegram Messenger App is Unsafe
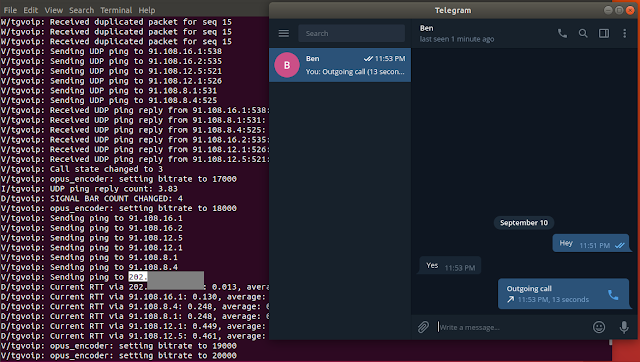
The bug was identified by security researcher Dhiraj Mishra. According to Mishra, the desktop version of the Telegram app was leaking IP addresses during voice calls made via a peer-to-peer framework. Smartphone users can turn off P2P calls by modifying the settings: Settings > Privacy and security > Calls > Peer-To-Peer but desktop users of Telegram aren’t offered this option.
It is worth noting that Telegram uses P2P framework to establish a direct connection between the two users when a voice call is to be initiated, and due to the bug the IP addresses of both the participants were being exposed.
Telegram offers two unique features namely Secret Chat and Nobody. Through Secret Chat, users can enable end-to-end encrypted calls/chats while with Nobody option users can prevent their IP addresses from being exposed during voice calls. When someone enabled Nobody option, the voice calls are routed through Telegram’s servers. Mishra identified that Nobody option isn’t available for desktop users, which means the location of every desktop app user will be vulnerable to exposure and all an attacker needs to do to obtain someone’s IP address is to make a call. As soon as the call is picked, the IP address gets revealed.
Patch issued
When Mishra reported his findings to the company, the issue was patched immediately in 1.3.17 beta and 1.4.0 versions of Telegram for Desktop. With this patch, the desktop version of the Telegram app will now be offering the Nobody feature too. You can enable it by clicking on this option: “P2P to Nobody/My Contacts via Settings → Private and Security → Voice Calls → Peer-To-Peer to Never or Nobody.
Telegram boasts of a worldwide fan following with a whopping 200million active users as of March 2018 and it is touted to be an ultra-secure messaging app that lets users make secure voice calls over the internet. But the discovery of a vulnerability in the most hyped feature of the app in its official desktop version does raise concerns. Classified as CVE-2018-17780, the vulnerability affected Telegram’s desktop app for Windows, Mac, and Linux OS.