The WannaCry ransomware attack is still infecting unsuspecting users, hospitals, and businesses around the world. While some users on Twitter are claiming they have already paid victims a massive amount of ransom money and are still waiting for the decryption key; the cyber criminals behind the whole campaign are still sending new messages in the shape of popups to their victims encouraging them to pay the ransom to get their files “more quickly.”
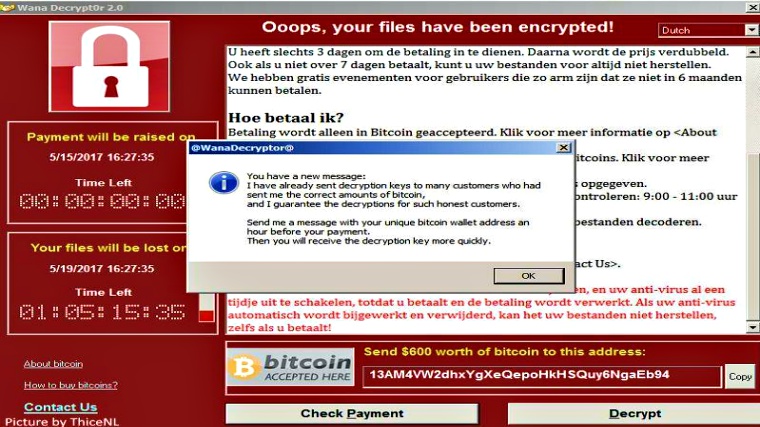
The message reads:
- “I have already sent decryption keys to many customers who had sent me the correct amounts of bitcoin, and I guarantee the decryptions for such honest customers. “Send me a message with your unique bitcoin wallet address an hour before your payment. “Then you will receive the decryption key more quickly.”
Here’s a full preview of the popup message:
The malware infection began spreading on Friday and so far more than 200,000 victims in 150 countries have fallen prey to the attack. The security researchers believe that the message could be pre-timed to appear on victims’ device but it doesn’t indicate if paying them will get their files back.
It must be noted that the first victim of WannaCry ransomware attack were computer systems at National Health Service (NHS) facilities and hospitals in the U.K. The doctors and IT staff was locked out from their computers and emergency patients was being diverted. Initially, the cyber criminals demanded a sum of $300 but lately, the amount has been increased to $600 in Bitcoin.
A Twitter bot watching the bitcoin wallets tied to the WannaCry ransomware attack shows that at the time of publishing this article the cybercriminals behind this attack have received 280 payments totaling 45.95330875 BTC which is $84,094.44 USD).
The three bitcoin wallets tied to #WannaCry ransomware have received 280 payments totaling 45.95330875 BTC ($84,094.44 USD).
— actual ransom (@actual_ransom) May 18, 2017
The IT security community, however, killed two working variants of WannaCry ransomware within two days of attack yet it only halted its spread temporarily. Remember, the WannaCry attacks were made possible with the NSA hacking tool leaked by Shadow Broker and an existing vulnerability in Windows’ SMB (Server Message Block Protocol). At the same time, Microsoft has urged users to update their systems to the latest version and also criticized NSA and the CIA for not sharing the vulnerabilities they found in the systems.
While Microsoft blames others; it’s time for users to update their systems right now, always keep a back of your data and avoid paying ransom payment to the criminals since there is no solid proof that victims have received the decryption key or not.
DDoS attacks are increasing, calculate the cost and probability of a DDoS attack on your business with this DDoS Downtime Cost Calculator.