Malicious threat actors are using exclusively designed URLs to deceive users into providing their Gmail credentials. This latest phishing campaign, discovered by security experts, utilizes a very effective phishing attack that can trick even the most alerted users and tech-savvy people.
The campaign involves sending infected messages to the contacts from an already infected computer. This message seemingly contains a simple PDF file that is previewed from Gmail directly. Once the recipient clicks on the attachment, it leads to a Gmail phishing page.
Read More: Hacker finds flaw in Gmail allowing anyone to hack any email account

The URL that appears after the attachment is opened is as follows:
“data:text/html,https://accounts/google.com”

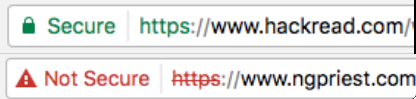
When loaded, the web browser doesn’t display any certificate warning at all. According to security researchers, there are white spaces evident in the URL due to which the victims cannot identify suspicious strings. Resultantly, an obfuscated script gets opened in a new tab.

Must Read: Gmail to Alert Users Upon Receiving Unencrypted Messages
WordFence published a blog post explaining how this phishing attack works:
“You click on the image, expecting Gmail to give you a preview of the attachment. Instead, a new tab opens up and you are prompted by Gmail to sign in again. You glance at the location bar and you see accounts.google.com in there. It looks like this….Once you complete sign-in, your account has been compromised.”
Currently, it isn’t clear if these malicious threat actors have identified some way to automate this entire process of accessing compromised accounts and spread the infection. The only way to prevent your account from being compromised is by enabling two-factor authentication or 2FA on Gmail. Also, never click on a link sent by unknown senders and avoid downloading and clicking on files coming from unknown senders.
Google was already notified about this new tactic of using Gmail URLs to trap innocent users way back in March 2016. The company is trying to find a way to prevent such attempts involving Gmail. This is why the Chrome security has introduced a Secure and NotSecure tag in the address bar.
Also Read: Hacking email accounts; a piece of cake with a social engineering trick