Romanian hackers used Bash Bug flaw to hackYahoo servers, according to a recent security news update.
Jonathan Hall, President of the IT consulting firm, Future South Technologies and a security researcher, has affirmed that a group of Romanian hackers used the Shellshock vulnerability to compromise Yahoo servers, which was also confirmed by Yahoo!
Hall said that the cybercriminals used Google search engine to identify vulnerable servers and built a botnet by exploiting the Shellshock flaw.
Bash Bug is a remotely exploitable vulnerability that affects Linux and Unix command-line shell (GNU Bourne Again Shell abbreviated as Bash). Discovered by security researcher, Stephane Chazelas at Akamai, the flaw allows users to send commands on Unix and Linux systems by connecting over SSH or telnet. It can also act as CGI scripts parser on a web server.
Related News: Shellshock Bash Bug Leaves Almost Every User on The Internet Vulnerable
The vulnerability gives both administrators and attackers enormous access to operating system features.
“The potential is enormous – ‘getting shell’ on a box has always been a major win for an attacker because of the control it offers them over the target environment,” said software architect and Microsoft MVP Troy Hunt.
The attacker, through the shell, could dump all data stored on the server, change its settings, or infect machines through malicious codes.
Hall noticed that the Win.zip domain was being used by the hackers to identify other servers that could be compromised using the Bash Bug flaw. He alerted the WinZip about it, but has received no response from them so far.
Hall found evidence that the Romanian hackers had compromised Yahoo servers and were trying to breach Yahoo! Games servers, which contain sensitive data of millions of players.
“Some of my observations indicate that him and his little Romanian cohort in there are also working towards another goal on Yahoo!’s network: the Yahoo! Games servers. One might wonder why they would bother going for that… Well, those games are visited by MILLIONS of people per day, and they’re also Java based. Think about it and you tell me why someone would want to compromise those,” said Hall.
He also identified two of the Yahoo’s servers that were compromised by the hackers.
“The following two servers have been 100% rooted successfully and confirmed by monitoring the groups actions: dip4.gq1.yahoo.com and api118.sports.gq1.yahoo.com.”
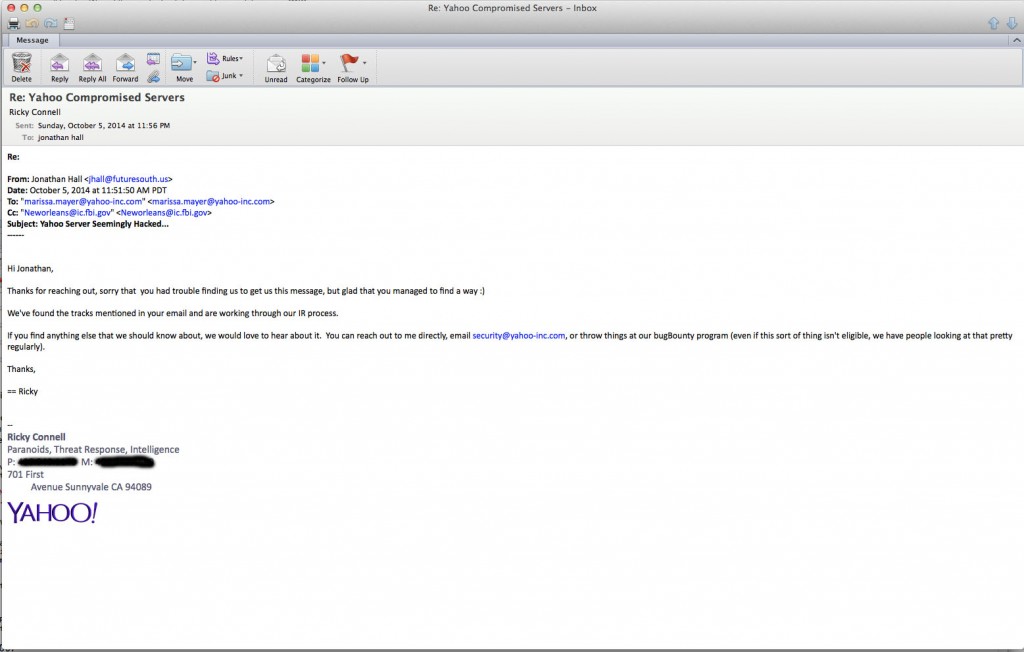
Yahoo! confirmed that three of their servers were breached through Shellshock vulnerability, in an email statement to Bloomberg Businessweek; however they also confirmed that no data were stolen.
“As soon as we became aware of the issue, we began patching our systems and have been closely monitoring our network, we isolated a handful of our impacted servers and at this time we have no evidence of a compromise touser data.” As soon as we became aware of the issue, we began patching our systems and have been closely monitoring our network,” said a Yahoo! said Yahoo spokesperson Elisa Shyu.
Although Yahoo! has patched its security breach, many other vulnerable servers still exist, said Hall.
“Last night, we isolated a handful of our impacted servers and at this time we have no evidence of a compromise to user data. We’re focused on providing the most secure experience possible for our users worldwide and are continuously working to protect our users’ data,” confirmed the official.
It’s funny how the high profile company like Yahoo is always vulnerable to any bug that comes around. Last time it was Yahoo that got vulnerable to Heartbleed bug putting users at risk and now Bash Bug has made its way deep inside the Yahoo servers.