Originally this Russian website was designed for purely non-controversial spear-fishing activities, but now its log-in page has been compromised and displays a phishing page.
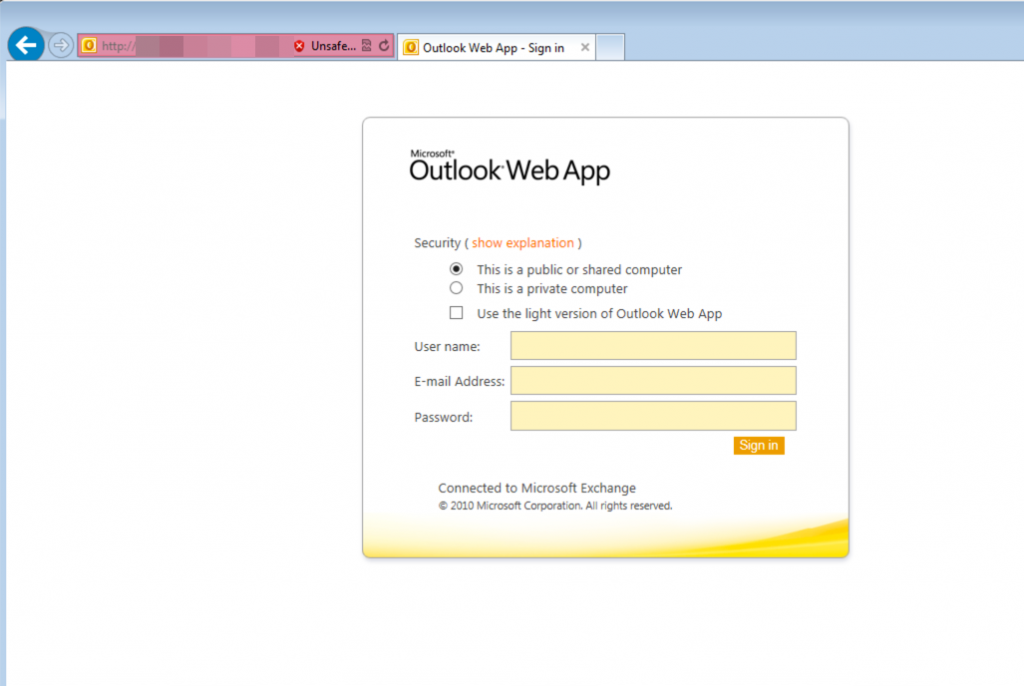
The agenda of this campaign is to steal login details of Outlook Web App.
Read More: Your Office Document may be Vulnerable to Malware: Warns Microsoft
The Scam:
According to security researchers who have been observing this campaign, the target was university students and an educational institution.
This scam relied upon a very real-looking fake page for tricking unsuspecting students, staff and faculty members. Attacker’s motive was to get the Outlook Web Access credentials leaked.
One significant difference between the real and fake log-in page was that to access account the fake one additionally asks for entering email address while the real one just needs username and password.
Users must note that in most cases this log-in information is used for accessing other accounts.
According to ProofPoint, if even one user gets fooled by this fake page, the hacker can access valuable information and may even access other resources.
As a result, attackers can easily retrieve financial information of confidential data as they can move laterally through the network.
In this spear-fishing email scam the security company hasn’t been able to reveal the bait yet. However, if the quality of this fake page is considered, the chance is high that it involves social engineering proficiency.
It is important that users check the URL of every log-in page before providing personal information. Special care should be given if the URL comes through email or from an unknown source.