On 29th July 2015, we reported how a group of anti-abortionist hackers hacked into the servers of Planned Parenthood, a pro-abortion organization.
Now, the same hackers have conducted a massive DDoS attack on the organization’s website forcing it to go offline.
The cyber attack was apparently conducted in the wake of controversial videos revealing that the organization is involved in the donation of fetus organs, tissues and various other body parts from unborn babies to the medical research facilities. However, it is a legal practice but highly controversial issue too.
Using Drone for Abortion: Here Comes The Abortion Drone
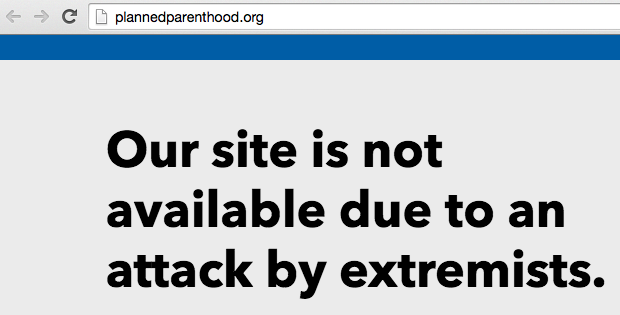
Planned Parenthood also tweeted about the cyber attack labeling the hackers as anti-abortion extremists.
BREAKING: http://t.co/Q8cXe58njh health website is under attack by anti-abortion extremists.
— Planned Parenthood (@PPFA) July 29, 2015
Earlier this morning users visiting the site were directed to a message “Our site is not available due to an attack by extremists.”
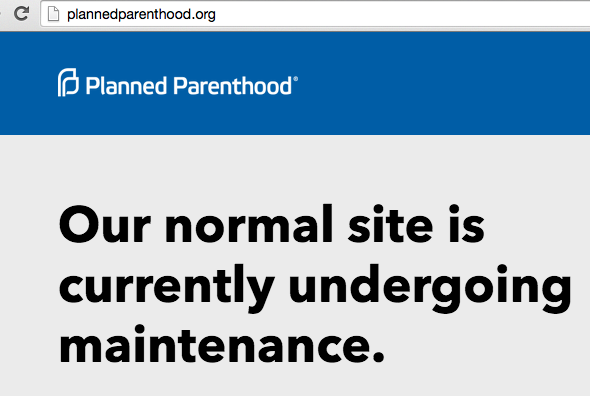
After few hours, another message appeared updating users that “Our normal site is currently undergoing maintenance.”
In an email conversation with Executive Vice President of Planned Parenthood Dawn Laguens told Wired that,
“Today, the Planned Parenthood websites experienced a wide scale distributed denial of service (DDoS) attack, a hacker tactic to overwhelm websites with massive amounts of traffic to block any legitimate traffic from getting in.”
The “anti-abortion extremists” hackers behind this DDoS attack previously breached into the servers of the organization and leaked the compromised data online.
To hack into the Planned Parenthood’s servers, the hackers used an attack known as “Blind SQL,” which reportedly exploits hidden error message returned from a site database. This attack is called blind because the attacker isn’t required to get the error messages to accomplish the attack.
At the time of publishing this article, the Planned Parenthood’s website was down for maintenance.
Report typos and corrections to [email protected]