Browsing Tag
Bluetooth
23 posts
Bluetooth Vulnerability Enables Keystroke Injection on Android, Linux, macOS, iOS
Another day, another Bluetooth vulnerability impacting billions of devices worldwide!
December 8, 2023
Researchers Jailbreak Tesla Vehicles, Gain Control Over Paid Features
The technical details of these findings will be unveiled at Black Hat USA on Wednesday, August 9, 2023.
August 4, 2023
BleedingTooth Bluetooth vulnerability allows RCE in Linux devices
Bluetooth has been for long, one of the most used communication protocols due to the ease it offers but that can be vulnerable as well.
October 16, 2020
BLURtooth vulnerability exposes devices to MITM attack
The attacks carried out by exploiting BLURtooth vulnerability are being referred to as the BLUR attacks.
September 10, 2020
Smart Lock vulnerability can give hackers full access to Wi-Fi network
The vulnerability exists in the August smart lock Pro + Connect model which hasn't been fixed.
August 12, 2020
BlueRepli attack lets hackers bypass Bluetooth authentication on Android
The findings related to Bluerepli were shared by researchers at the Black Hat USA 2020 virtual event.
August 7, 2020
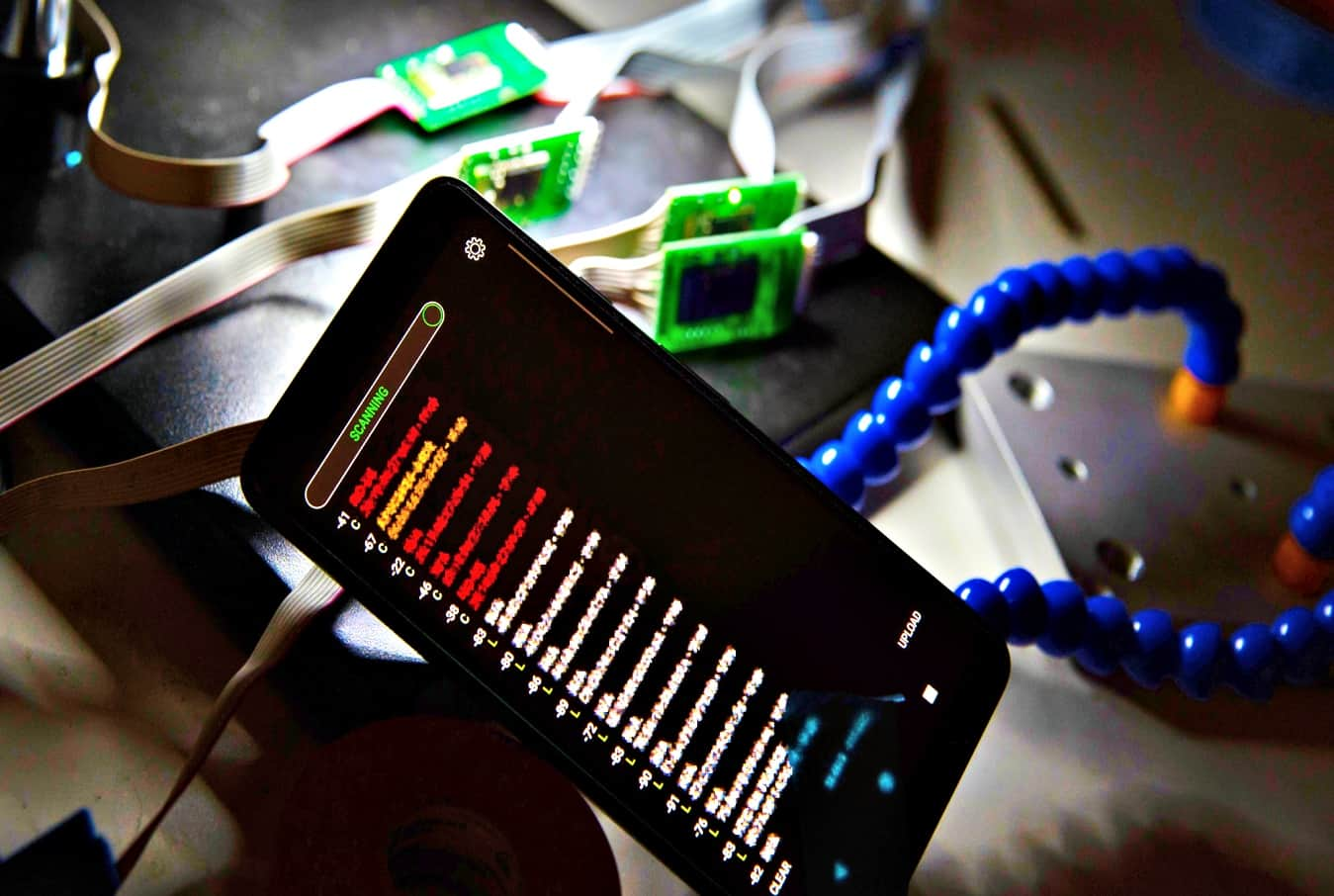
Bluetana app detects gas pumps card skimmers in 3 seconds
Bluetana takes 3 seconds to detect illegal card skimmers, unlike law enforcement agencies who can take up to 30 minutes for inspection.
August 17, 2019
New Samsung Galaxy S10 review and features
The all new Samsung Galaxy S10 family has been released by Samsung on 8th March, 2019 and despite…
March 13, 2019
Update your devices: New Bluetooth flaw lets attackers monitor traffic
The Bluetooth flaw also opens door to a man-in-the-middle attack. The IT security researchers at Israel Institute of Technology have discovered a…
July 25, 2018
DNS rebinding attack puts half a billion IoT devices at risk
Armis, an Internet of Things (IoT) security vendor and cyber-security firm, reports that about half a billion smart…
July 21, 2018