Ever wondered about the number of users an Android-based malware app can infect after getting approved and published on the Google Play Store? Thousands or maybe around few hundred thousand?
But, in this case, your speculations must have nosedived because a recently detected malware app has already managed to infect up to one million Android users, a recent analysis by the Middle East based IT security firm ESET reveals.
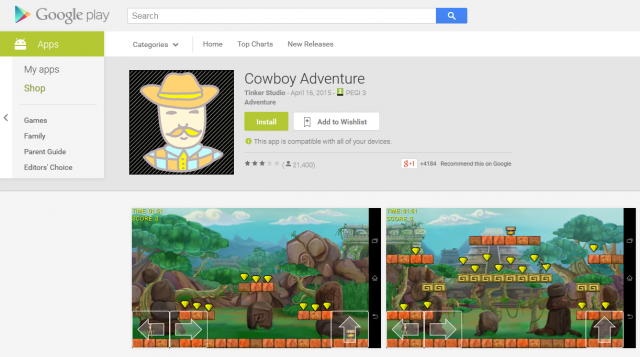
Report reveals 1 in every 5 Android Apps is MalwareBelieve it or not, a phishing malware was enclosed in a popular gaming app that goes by the name of “Cowboy Adventure,” used to compromise the user’s Facebook credentials. It is a simple but relatively popular game that make use of 2D game engine “Platformer 2D.”
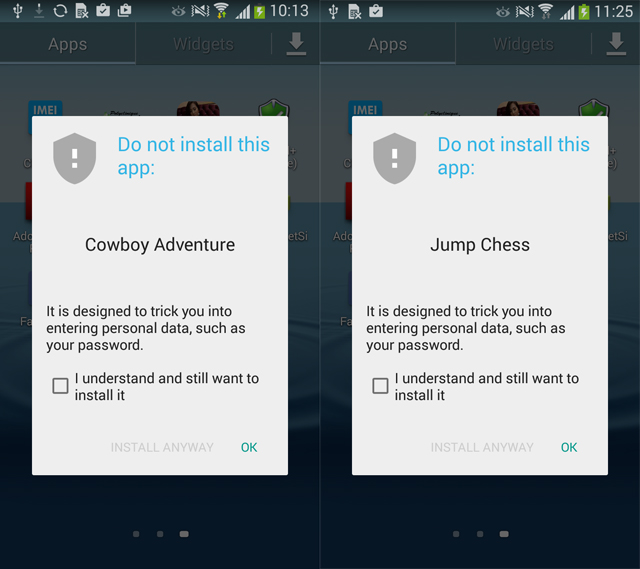
The security and malware researchers detected these apps as Trojan named “Android/Spy.Feabme.A”. There were two apps on Android Play Store that contained the same malicious functionality, one was “Cowboy Adventure” and the other one was “Jump Chess.” And the developers of these gaming apps used it as a tool to collect Facebook IDs and passwords of the users.

What’s Actually Happening behind These Malware Apps?
Actually the working of both of these apps are similar to the BatteryBot Pro app we recently reported about. That means these malware comprising apps did work as genuine apps but additionally they used to fraud with the users.
During installation, the app didn’t request for any suspicious permissions, but after successful installation once the app has been launched by user, a phishing activity is logged i.e. the app pops up a fake Facebook login screen.
If the user is novice and didn’t pay close attention to the screen then it is most likely that the user will fell for the trick and enter their Facebook username and password, which would be instantly sent to the hacker’s server.

However the total number of possible victims might be one million but the good news is that some of the users were not tricked by the scam because either they saw user reviews on Play Store or they were experienced.
Hackers Develop Android Malware Every 17 Seconds“Despite the fact that the number of potential victims may have been up to one million, thankfully many were able to avoid being tricked by this scam as the negative user comments helped prevent them from entering their Facebook username and password,” – Robert Lipovsky, Senior Malware Researcher at ESET.
Removal of Apps from Google Play Store
Both of these malware apps was developed by the same developer and the good news is that both were removed by Google from their Play Store last week. In addition to that, if a user tries to install these infected apps through another source, Google will show a warning message that suggests them not to install the app.
At the time of removal, the Cowboy Adventure was at version 1.3 which was released on April 16th. Since then the malware app was being served to the users, compromising their Facebook credentials.
Whereas, on the other hand, Jump Chess was available on Play Store since April 14th and was downloaded on about 5000 devices. So this app wasn’t able to infect large audience as compared to Cowboy Adventure.
Steps Taken To Further Protect Android Users
Google said that they are working on improving their security mechanisms for Android users which will lower the risk of infection by these malware apps.
Lipovsky also recommended a couple of safety steps for Android users i.e. the user should download the app from official sources like Google’s official Play Store. Before downloading, users should also make sure to read reviews posted by other users.

We will also recommend you to make use of two-factor authentication services that are being provided by most of the online websites. It adds a new layer of security while making it harder for hackers to get access to your account – in case your account credentials gets stolen.
Report typos and corrections to [email protected]
WLS
ESET






