In February this year, HackRead published a detailed report on Proton malware which targets macOS. At that time, the malware was being sold on a Dark Web marketplace for 40 BTC ($41,891 at the time of sale). The same malware then showed up last month infecting Mac users who download Elmedia Player.
On November 20th, the IT security researchers at Malwarebytes Labs discovered attackers using fake Symantec blog website to deliver Proton malware against unsuspected macOS users. On the site, the cybercriminals published an “analysis” discussing the existence of a phony malware threat called CoinThief.
The analysis went on to explain how CoinThief was discovered in 2014 and how users can protect themselves against this threat by installing “Symantec Malware Detector,” a program that does not exist. In reality, the download file was Proton malware created to infect devices and steal data.

According to the blog post by Malwarebytes Labs‘ director of Mac & Mobile Thomas Reed stated that: “The site is a good imitation of the real Symantec blog, even mirroring the same content.The registration information for the domain appears, on first glance, to be legitimate, using the same name and address as the legitimate Symantec site. The email address used to register the domain is a dead giveaway, however.”
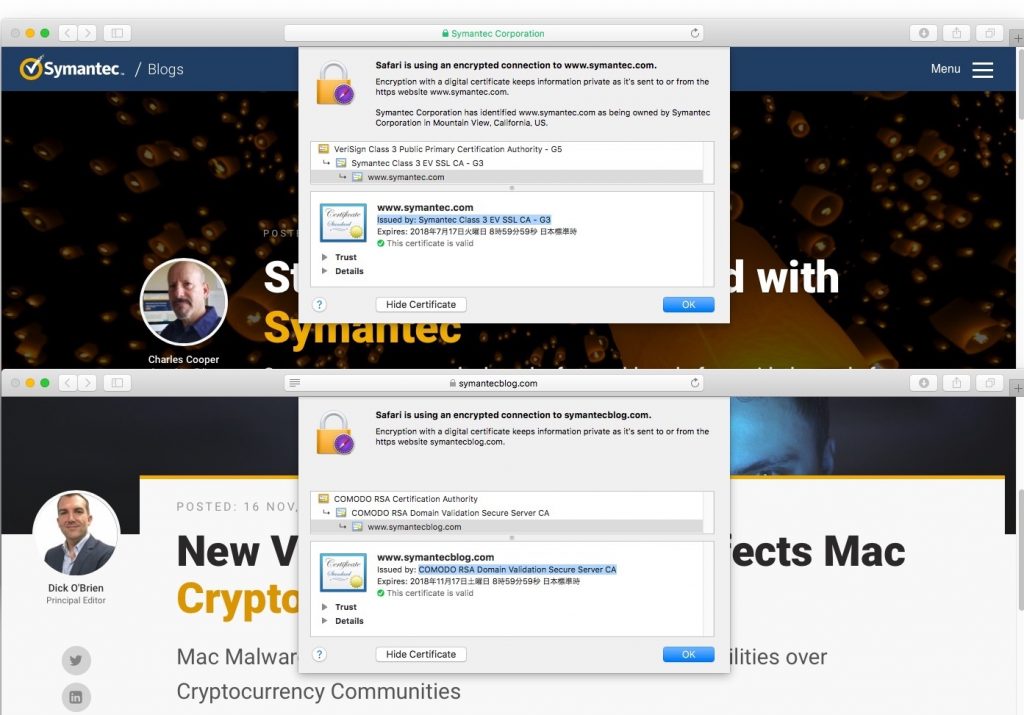
Reed further found that attackers also created fake Twitter profiles to spread the scammy website on the social media site however some authentic users were also retweeting the link. But what is worth noting is that the site was using SSL certificate issued by Comodo cybersecurity firm and not by Symantec.
Those users who installed the file on their Mac devices might be under threat since Proton malware can take root-access privileges and allow an attacker to obtain complete control of a targeted device. It also runs real-time console commands and file-manager, keylogging, SSH/VNC connectivity, screenshots, webcam operation and the ability to present a custom native window requesting information such as a credit card, driver’s license and more.
Proton also boasts the capability of iCloud access, even when two-factor authentication is enabled. The malware is shipped with genuine Apple code-signing signatures. This means the author of Proton RAT somehow got through the rigorous filtration process Apple places on MAC OS developers of third-party software and obtained genuine certifications for his program.
Since Apple is already aware of the issue, it has revoked the certificate used to sign the malware. This will stop Symantec Malware Detector from further infecting users.
“Since Proton is designed to steal login credentials, you will need to take some emergency actions post-infection,” said Reed. “You should treat all online passwords as compromised and change them all. Be sure, while you’re at it, to use different passwords on every site, and use a password manager (such as 1Password or LastPass) to keep track of them. Since 1Password vaults are a target of Proton, be sure that you don’t store your password manager’s master password in your keychain or anywhere else on the computer. That should be the one and only password that you memorize, and it should be strong.”
The good news is that after Malwarebytes Labs discovery, the fake website vanished into thin air after the company suspended its hosting account. However, this does not mean that attackers cannot come back with yet another fake domain under the name of popular cybersecurity company.
Also, since malware attacks against Mac devices are increasing users should not downloaded apps and software from third-party platforms. Moreover, use authentic security apps, scan your device on a daily basis and follow these 11 tips to secure your Mac against such attacks.






