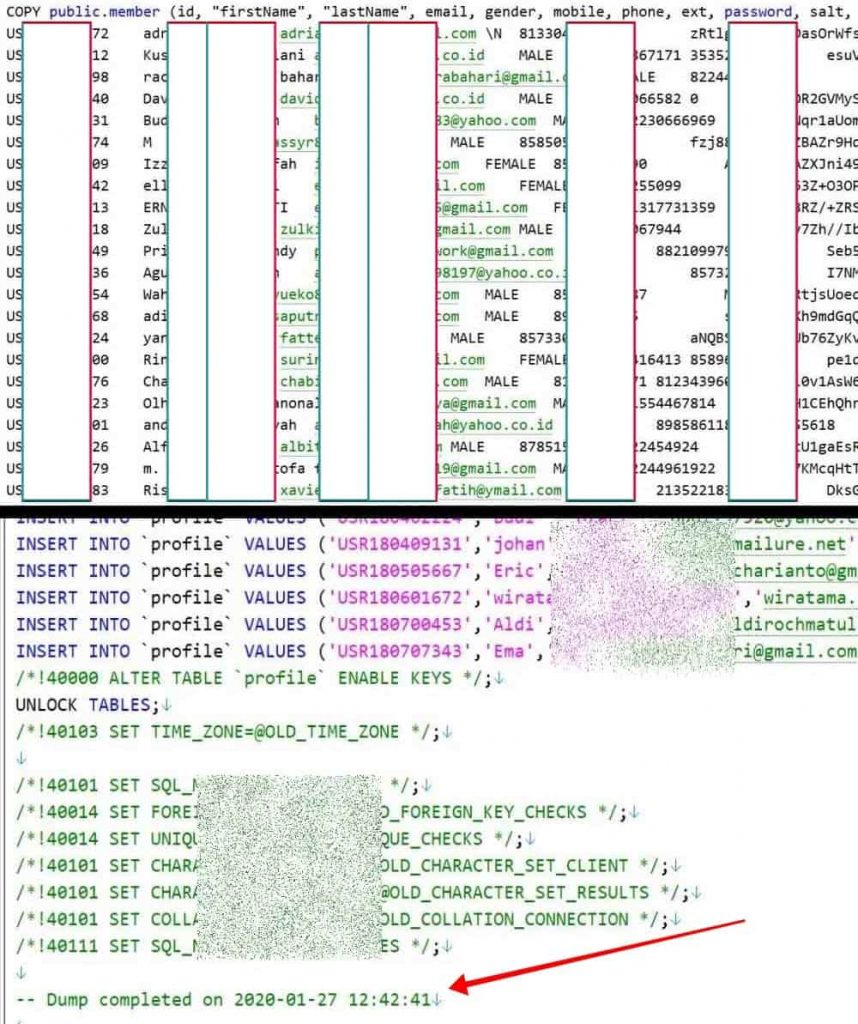
Exclusive: The sample data seen by Hackread.com suggests Bhinneka’s database was stolen in January 2020.
Mostly, when an attacker gains access to a database, they try to profit off it either through a ransom or by listing it for sale. Sometimes though due to reasons such as revenge or perhaps ol’ fashioned fun, attackers dump the databases online making them freely available.
A case of the latter has emerged today when a hacker posted the database of one of Indonesia’s largest online store named Bhinneka on a hacker forum.

The database was initially hacked on 27 January earlier this year but has now been put out in the open by the attacker. The downloadable folder contains 2 SQL files which contain the records of approximately 1,262,300 accounts in totality.
Just In: Database with 271 million Wattpad accounts leaked on a hacker forum
These worth 762 MBs include the following fields:
- Unique IDs
- Full names
- Email addresses
- Gender
- Contact numbers
- Passwords
- Address details
- Date of Births(DOBs)
- Social media IDs
- Log details such as the last login information
- Classification of whether the user is an admin or a staff member which also hints that the database may include employee details.
An interesting and perhaps comforting aspect though is that one of the fields is labeled as “Salt”. This means that whoever obtains access to the data will have a hard time cracking the passwords through brute-forcing prolonging the process.
On the other hand, this is not the first time that we’re seeing the data breach of a large Indonesian store. Just over a couple of months ago in May 2020, the data of 91 million users were exposed from Tokopedia – an Indonesian giant – was listed for sale for a mere $5000 by ShinyHunters hackers.
Hackread.com can confirm that the same Tokopedia hackers are behind the Bhinneka breach.
Then a few weeks later, a trove of data amounting to 2.3 million Indonesian Citizens was leaked by another threat actor marking back-to-back damages on the cyber-front for the country.
See: 142 million MGM customers’ data sold on dark web marketplace
To conclude, users of Bhinneka are advised to immediately reset their account passwords and make sure they are not re-using the same password on other sites. Furthermore, they should be on the lookout for any phishing campaigns that any malicious actor who accesses the data can plan to engage in.
Did you enjoy reading this article? Do like our page on Facebook and follow us on Twitter.
