An ethical hacker, security researcher and a writer Rafay Baloch was paid total USD 10,000 for reporting a Code Execution / Command Execution vulnerability on the sub-domain of Paypal.
Paypal had started a *Bug Bounty program* for security experts around the world to report any bug or vulnerability is found on their server.
The hacker writes on his official blog that while testing Paypal’s server, he found a critical command execution vulnerability allowing hackers to execute any command on the server.
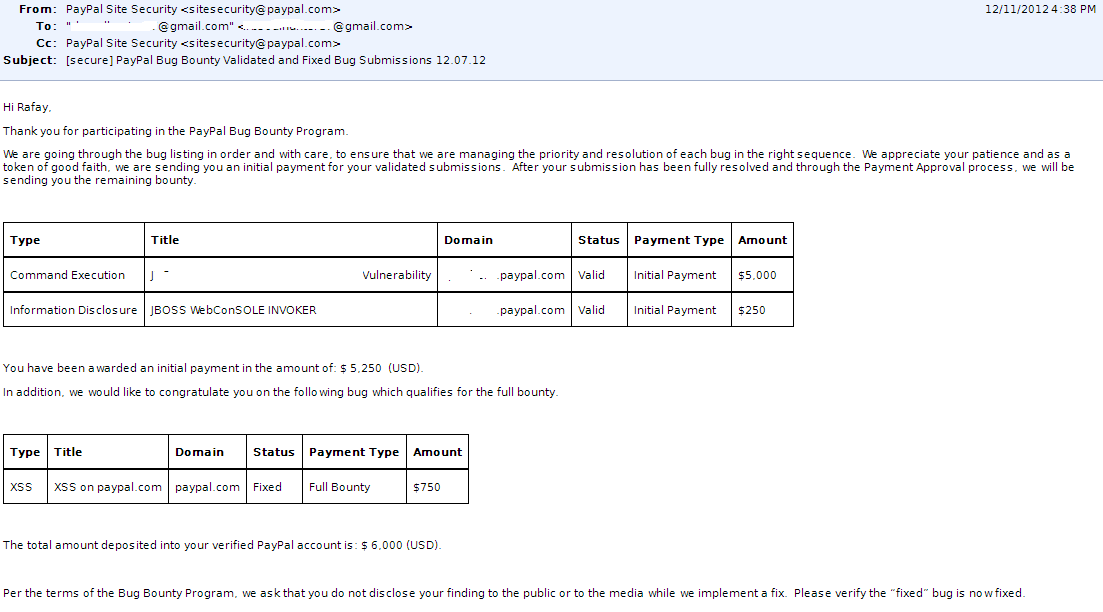
Rafay was initially paid USD 600 for reporting XSS Vulnerability on the main site of Paypal, later after reporting several other bugs, the company paid more USD 6000 for his expert services which obviously saved Paypal from a disaster and embarrassment.
Here is a screenshot of an email conversation between Rafay and a Paypal representative about money reward.
He claims that at the moment more then 20 of his reported vulnerabilities are still being validated by Paypal and it will not be a proper time to disclose the types of vulnerabilities.
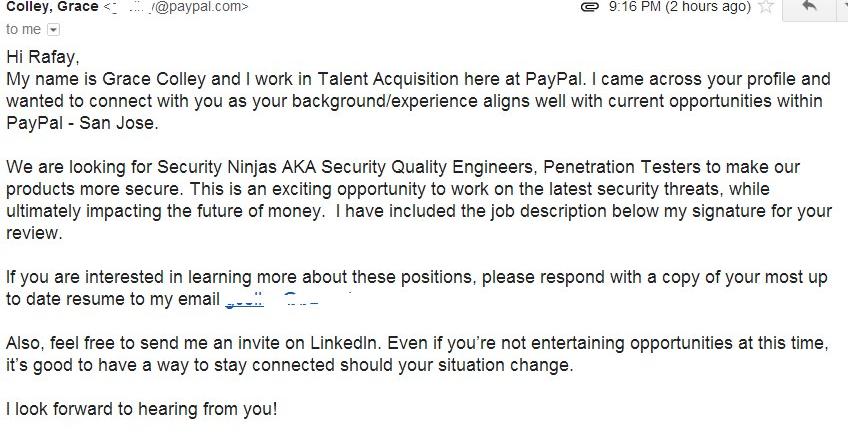
However, money is not the only thing awarded to Rafay, Paypal has also offered him a job as a Senior Pentester A.K.A SecurityNinja in their HQ in San Jose, USA.
Here is another screenshot of an email conversation between Rafay and a Paypal representative Colley Grace regarding job officer at PayPal.
Speaking with HackRead, Rafay said that:
He feels great and proud to serve his nation by providing the cyber world a secure future.
If you would like to contact Rafay Baloch, he is available on Twitter and of course, you can send him an email on his blog.








Thanks for spreading the word.
Warm Regards,
Rafay Baloch
You are my idol ^_^