The IT security researchers at ESET detected malware on popular Android games which created quite a furor among users.
A couple of weeks ago we reported how the hackers are infectiting verified Android apps with malware and successfully passes through Google Bouncer, the vetting system of Google Play Store.
Now, ESET reports that the malware was discovered on a number of these games and were said to be directly downloaded from the Google Play Store.
Games such as Candy Crush, Plants vs Zombies and others were known to be infected with the malware capable of exposing your Android device and give the attacker control over it.
Initially, such games came with external software and applications such as resources or system data. This raised a red flag as many felt that there should be no reason for such red flags as these games were downloaded through Google Play Store, which is a legitimate portal.
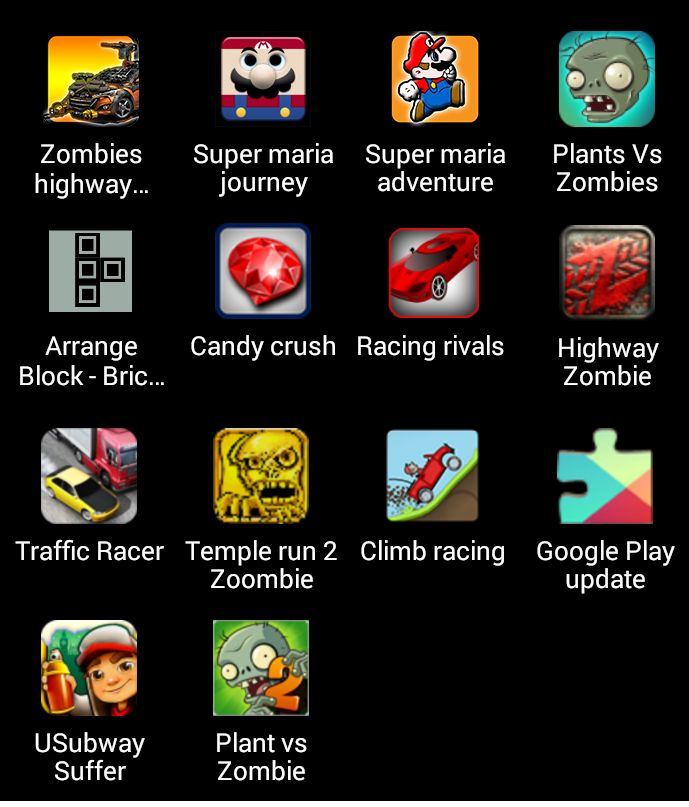
Infected applications:
The Trojan took two to three days to be activated, which could be how it passed through Google’s detection system. Google has this protection screening software against such applications in games. The time that it took to activate also proved to be misleading for many users. They might have downloaded it thinking it was just a harmless application and nothing to be concerned about.
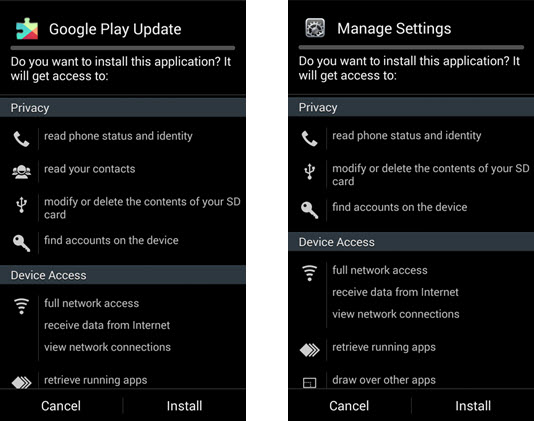
Once downloaded it asked for permission to administration rights in the device and when granted these, it began to communicate with its C&C server.
Referred to as Android or Mapin, it was known to be very damaging. Personal information and data were vulnerable, users lost control over content and were spammed, games and other software was downloaded and installed without access being granted.
It mostly works when full-screen adverts are displayed after a particular website has been opened on the device. This was a tricky situation for many. Experts at Eset stated that the Trojan passed through Google’s detection because of its functionality. While they also said that not all variables of the virus were fully operational and the effects were still to be seen.
The permissions:
The Trojan went undetected for a year and was then pulled by Google.
ESET has released a list of 20 most popular Android gaming apps carrying malware.
This is not the first time when a malware embedded Android app made it to Google Play store. In the past, a Fake BatteryBot Pro app was available on the store developed with the intention to hack users’ device.
ESET