The US Justice Department has charged two alleged members of Lizard Squad and PoodleCorp DDoSing group for online crimes.
Two 19-year-old men have been charged by the United States Department of Justice for conducting credit card theft and operating the powerful DDoS services to make websites go offline, namely Booter or Stresser, and compromising protected computers. The two males Zachary Buchta and Bradley Jan Willem Van Rooy, according to Feds, are allegedly part of the Lizard Squad and PoodleCorp hacking groups.
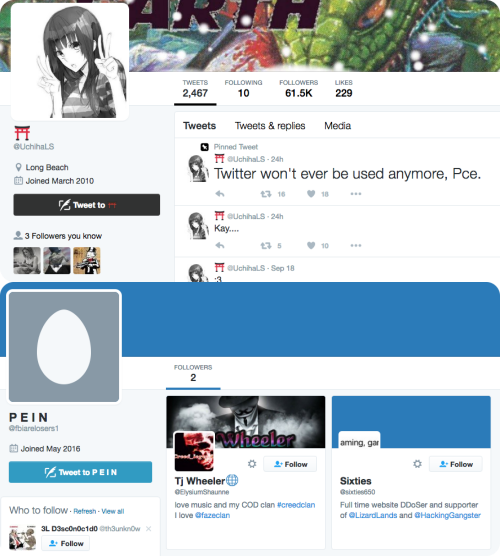
Buchta hails from Fallston, Md., while Van Rooy comes from Leiden, the Netherlands. The US Attorney’s office for Illinois issued a statement informing that Buchta used the alias “@fbiarelosers,” “pein,” “xotehpoodle” and “lizard,” to carry out malicious activities. Van Rooy used the nicks Uchiha,” “@UchihaLS,” “dragon” and “fox.” Both the members used to work with other members of the Lizard Squad and offered services for conducting cyber-attacks. They have facilitated countless DDoS attacks and “to traffic stolen payment card account information for thousands of victims,” the statement read.
Must Read: OVH hosting suffers 1Tbps DDoS attack; largest Internet has ever seen
PoodleCorp’s cyber-attack service called PoodleStresser utilizes an API (application programming interface) that has been designed by the vDOS proprietors. vDOS is a cyber-attack service that was taken down in September after two of its key operators were arrested. vDOS was hacked a few months back and KrebsOnSecurity shared a copy of the user database as well, which indicated that PoodleStresser was one of the key clients of vDOS and they targeted KrebsOnSecurity quite frequently.
Lizard Squad and DDoS:
The use of IoT devices as a botnet is not something new. Previously, Lizard Squad released a Linux-based DDoS tool LizardStresser which has been used to hack CCTV devices and use them to target high profile targets flooding them with as much as 400Gbps of data. The attacks were aimed mostly at gaming platforms, Brazilian financial institutions, ISPs, and government institutions.
https://twitter.com/LizardLands/status/719657893339881472
PoodleCorp and DDoS:
PoodleCorp was also promoting their DDoS tool these days and increasingly targeting IoT devices to build botnets to conduct DDoS attacks. The group has quickly made the name by DDoSing several gaming giants including, Pokemon Go, PlayStation, Electronic Arts (EA), Grand Theft Auto,Blizzard, League of Legends and GTA and PlayStation Servers.
As per the investigation of Feds, Buchta and Van Rooy operated similar services called phonebombernet. This website allowed customers to choose targets to send out harassing and threatening phone calls repeatedly from fake numbers for $20 per month. The duo would then call the victim’s number and used pre-recorded messages to harass the individual. The Justice Department has issued one of those pre-recorded messages, which is as follows:
“When you walk the fuc**** streets, Motherf*****, you better look over your fuc**** back because I don’t give a flying f**k if we have to burn your fuc* house down, if we have to fuc**** track your goddamned family down, we will f*** your sh** up (retracted) motherf***.”
Related: Meet Linux.Mirai Trojan, a DDoS nightmare
Furthermore, the complaint (PDF) files by the US Attorney’s office states that they also offered services of selling stolen credit cards and their credit card shop has around 347 pages of data of cards available for purchasing. A single page had ten records.
Buchta, who was arrested in Maryland, is due to appear in a court in Chicago on Wednesday. Van Rooy was arrested from the Netherlands and is yet to be extradited. They both might be getting ten years in prison if proven guilty.
US-DOJ