Google Chrome, Mozilla Firefox, and Opera browsers are known for their tight security measures, yet they are often targeted by malicious actors because of the fact that these are the most used browsers worldwide. As a result of the tight security measures, hackers have come up with a new technique to target users with a highly sophisticated phishing scam using “Unicode characters.”
The Perfect Phishing attack
A phishing attack usually depends on two things: a perfect disguise and somewhat the ignorance of users. But not this one as hackers are now faking popular domains like Apple, Google, or eBay on their own fraudulent websites. Hackers are even able to get the little “Secure” green bar for their fraudulent websites making the attack even more sophisticated.
If a user is on to one of these malicious sites, practically there is no way of telling that they are fake, and users can be easily fooled to put their credentials on the fake domain.

Nearly Impossible to detect
According to Mr. Xudong Zheng, a security researcher, Google Chrome has a dangerous new vulnerability that makes phishing attacks almost impossible to detect.”
He further added, “It becomes impossible to identify the site as fraudulent without carefully inspecting the site’s URL or SSL certificate.”
The Flaw-explained in Layman terms
According to security researchers, the flaw exists because of the inability of an encoder “Punycode” to render some character sets properly.
A Chinese character “a” and a Latin character “a” are rendered differently in the web-browser, however, on the surface bot, the characters look like a simple “a” in the URL bar, and this flaw can be easily exploited by hackers.
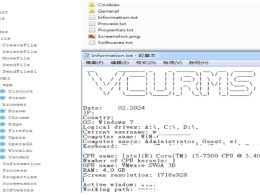
Mr. Xudong showed this critical flaw by creating a fake version of “Apple.com” website by using the domain name “xn--80ak6aa92e.com”. He chose foreign language characters and took advantage of the rendering mechanism of Chrome browser.


A relief
Mr. Zheng reported this flaw to the tech giants in January, and since then, the tech giants have been working on a possible patch to cope with this flaw. Google officials have already fixed this flaw in the latest beta release “Chrome Canary 59, ” and the update will be available worldwide on April 25th.
However, the same thing can not be said for the Firefox browser as the flaw has not been patched on it yet. But here is a temporary solution for Firefox:
* In the URL bar type “about: config” and press enter.
* Then, type “punycode” in the search bar of the browser.
* Now search for “network.IDN_show_punycode and change the value of it from false to True.
Until an official patch is released by the browsers, users are advised to type in the URLs manually and also to double check the website for any suspicious activity before putting in sensitive information.
DDoS attacks are increasing, calculate the cost and probability of a DDoS attack on your business with this DDoS Downtime Cost Calculator.