Spain’s largest radio station Cadena SER and IT service provider Everis suffered ransomware attacks which crippled its service.
While the protests in Catalonia may be or may not be a bad thing depending on who you ask, everyone in Spain would agree that what happened today is nothing short of unpleasant. Earlier this week, two of Spain’s largest companies were compromised by ransomware.
The first one which is Everis happens to be the country’s largest managed service provider and the second one – Cadena SER – the largest radio station in Spain.
See: Hackers infect Canon DSLR camera with ransomware
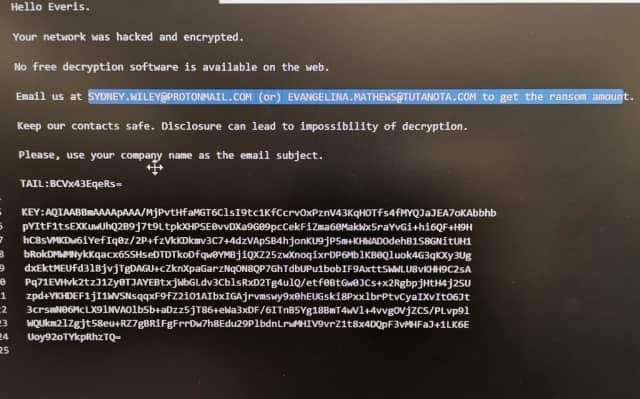
In initial news, it has been reported that Everis prompted employees to shut down their PCs after discovering they were under attack. A reason why the company did not initially publicly disclose the incident may be because of one of the requirements of the attackers asking them not to make any such move.
On the other hand, a note found on their system asked them to find out the payable amount by emailing them at s[email protected] or [email protected] with Everis – the company name – as the email subject.
According to reports, hackers have demanded €750,000 equivalent to $835,923 as a ransom to send the decryption key. As for how the company was infected in the first place, a cybersecurity consultant took to Twitter elaborating on the process.
Note: Translation of these tweets have been done using Google Translate.
Veo esta info online:
The threat phases are:
1. An everis user access to a compromised website where the source code was modified to show a fake browser update and download a file.— Arnau Estebanell Castellví (@ArnauEstebanell) November 6, 2019
Detailing further, he goes on to state,
1. The file is a JavaScript code (JS) that infects the device with a C2C malware categorized as “EMOTET.” This JavaScript creates additional exe files.
2. Once the attackers control the infected device, install a PowerShell post exploitation framework called Empire1. With Empire Framework in the infected device, the attacker enumerates the network and gets credentials from the infected device cache. With this, different Empire installations are seen in different hosts and servers.
4. Attackers distribute a ransomware family called “BitPaymer/IEncrypt” to Everis devices through compromised hosts and servers
On the other hand, the Cadana SER radio station was infected with unidentified ransomware forcing them to take all of their computers offline while continuing operations with the help provided by its headquarters in Madrid.
The attack was also confirmed by multiple national institutions including Spain’s Department of Homeland Security(DSN) and the Spanish National Cybersecurity Institute (INCIBE) with the latter currently helping them recover their data and get back online.
However, a disappointing aspect was found with how Spanish authorities tried to downplay the incident, particularly the DSN who went on to state that:
“This type of attack occurs quite frequently. In 2016, the National Cybersecurity Institute handled some 2,100 similar incidents.”
To conclude, companies have been increasingly targeted with ransomware over the past few years despite which some firms neglect cybersecurity throwing not only themselves but also the data of their customers into jeopardy. This can be of course be attributed to attackers coming up with better ways but at the same time, the emergence of cryptocurrencies and other anonymous payment methods has also eased ransom taking popularising this method.
See: How to Prevent Growing Issue of Encryption Based Malware (Ransomware)
To protect themselves, companies with substantial financial sources that would make up the majority of medium and large enterprises should hire dedicated cybersecurity teams. Sure, it will be a drain on their finances in the short term but if seen in the long run, it can help avert PR crises which far outweigh any other financial implications the firm may have in spending money for security.
Did you enjoy reading this article? Like our page on Facebook and follow us on Twitter.