The threat actor was also able to see the user’s transmitted data on the Tor browser in unencrypted format and tamper with it for their own ill-motives.
For users really concerned about government surveillance and privacy in general, the Tor browser offers a suitable escape anonymizing your internet activity. However, just like any piece of technology, it too comes with its flaws.
One of these is that the Tor network uses 3 different nodes or relays for any communication that occurs on it to hide the real source of the traffic. The last of these relays is an exit relay which gets to see where the data is being actually sent. Yet, what happens when this exit relay is malicious?
See: 8 best dark web search engines for 2020
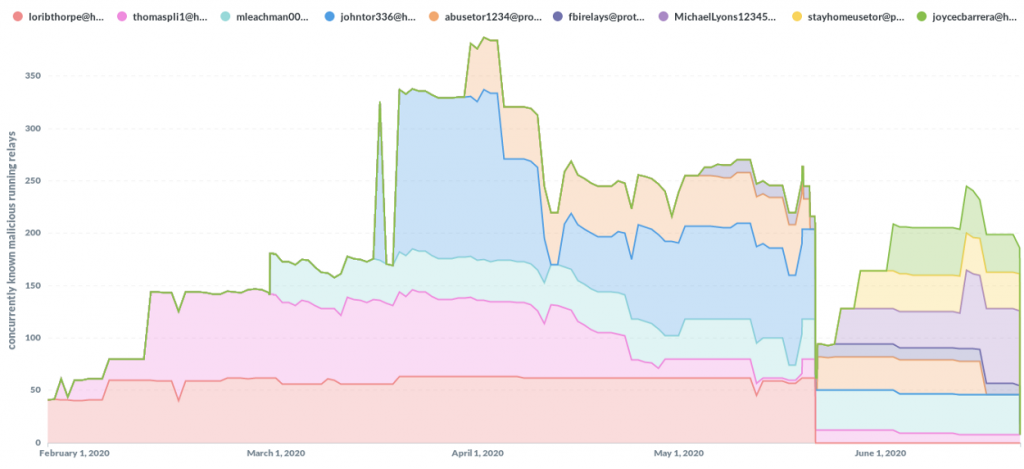
This is exactly what has been reported recently by a researcher going by the online handle of “nusenu” who found out that up to 24% of the exit relays on the Tor browser were being controlled by a single threat actor up to May 2020 which placed an enormous amount of power in one hand.
This allowed this threat actor to see the user’s transmitted data in unencrypted form and therefore tamper with it for their own ill-motives. One way they did so was by changing the original Bitcoin addresses of users and replacing them with their own in order to steal the coins being transferred.
Explaining in detail, the researcher states in their blog post that,
They perform person-in-the-middle attacks on Tor users by manipulating traffic as it flows through their exit relays. They (selectively) remove HTTP-to-HTTPS redirects to gain full access to plain unencrypted HTTP traffic without causing TLS certificate warnings. It is hard to detect for Tor Browser users that do not specifically look for the “https://” in the URL bar.
The good thing though is that till now, a sizeable portion of the malicious relays has been taken down. The downside is that still, about 10% of these relays are active placing a lot of users at risk.
See: Fake Tor browser stole Bitcoins from dark web users
For the future, it is up to the Tor project’s management and community to raise their voice on this particular issue and be more vigilant about removing such actors from the ecosystem.
On a parting note, Hackread.com would like to remind readers that according to the author, things do not seem to be improving for good in the future as the researcher states:
After the blog post from December 2019 the Tor Project had some promising plans for 2020 with a dedicated person to drive improvements in this area, but due to the recent COVID19 related layoffs that person got assigned to another area. In addition to that, Tor directory authorities apparently are no longer removing relays they used to remove since 2020–06–26.
This should be alarming considering that many look solely to the Tor browser to protect their privacy. A suitable method to tackle this issue may be to require a real-world-identity verification of those who wish to run a relay so that the concerned authorities could take action against them in the case that any malicious activity is found to be occurring.
Furthermore, cryptocurrency sites also need to take security measures accordingly considering that they are a frequent target.
Did you enjoy reading this article? Do like our page on Facebook and follow us on Twitter.

Trust trusted browsers that care about their own and your safety – Utopia Ecosystem!
I sleep well and you?)