Yahoo ad network has been exploited by a group of hackers that resulted in a serving of malware and ransomware adverts on Yahoo.com and its sub-websites including news, finance, sports, celebrity and games.
The hackers found a vulnerability in the ad network and managed to run an advertisement campaign, which was targeted towards hundreds of millions of people to infect their computers.
Hackers Sending Fake Windows 10 Upgrade Ransomware Email, Encrypts Every File

The security researchers at Malwarebytes revealed that the hackers behind this campaign are the same who were previously involved in exploiting vulnerabilities found in Adobe Flash plugin. They also found out that the Angler Exploit Kit was used by hackers to leverage this malvertising attack.
For those who don’t know, Angler Exploit Kit is easy to use software package for malware attacking. This kit has been dominating the malware attacks being carried out since past ten months and the kit has seen a significant increase in the growth of its market share. The said kit is capable of handling various malware activities including ransomware, backdoor Trojans, rootkits and many others.
Just like most of the malware attacks, exploit kits are used by hackers in this attack in an attempt to redirect the targeted user to a website infected with malware. However, most often it is observed that these spoofed websites infect a user with ransomware, which once executed would encrypt every file of the victim’s computer and the decryption code would only be provided when the hacker has been paid with the ransom amount within the specified time.
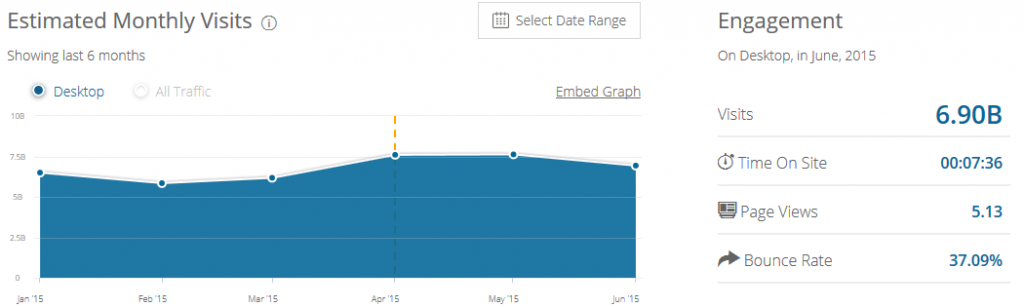
According to the statistical data provided by the SimilarWeb, the entire Yahoo network received approximately 6.9 billion visits, during the month of June, from desktop devices. While the malvertising campaign began on July 28th and was in operation until August 3rd, which means it was actively running on the Yahoo network for almost a week, affecting millions of website visitors.
Of course, that is a huge number of vulnerable users. The effect of this advertisement campaign is still not revealed, but malvertising campaigns like these usually include both ransomware and ad fraud malware. However, there was a great chance that you could have been infected by this malware because it does not require any interaction from the user side to initiate an attack. Malvertising is a silent killer.
According to the researchers over at Malwarebytes:
“While there is no way to know for sure who may have been exposed to the rogue adverts, the sheer numbers thrown at the Yahoo pages could potentially mean high rates of infection. Many Malvertising attacks tend to focus on specific geographical locations depending on ad networks used, but this campaign could have had a huge amount of reach.”
Update:
After the story was published on the Internet, Yahoo’s spokesperson responded with the following statement:
“Yahoo is committed to ensuring that both our advertisers and users have a safe and reliable experience. As soon as we learned of this issue, our team took action to block this advertiser from our network.
We take all potential security threats seriously. With that said, the scale of the attack was grossly misrepresented in initial media reports and we continue to investigate the issue.
Be careful what you click on
Unfortunately, disruptive ad behavior affects the entire tech industry. Yahoo has a long history of engagement on this issue and is committed to working with our peers to create a secure advertising experience. We’ll continue to ensure the quality and safety of our ads through our automated testing and through the SafeFrame working group, which seeks to protect consumers and publishers from the potential security risks inherent in the online ad ecosystem.”
In past, Youtube and Monster Jobs were also targeted with malvertising attacks.
Report typos and corrections to [email protected]
Malwarebytes