A group of security researchers turned a working webcam into a backdoor allowing attackers to remotely connect themselves with the device.
The dangers of hackable Internet of Things (IoT) devices are various and wide-ranging and it is becoming more and more likely that such devices get hacked through some simple engineering skills. Recently, the Vectra Networks researchers carried out an experiment in which they transformed a D-Link DCS 930L webcam into a backdoor device.
The device became capable of spying on the local network of a target without leaving any clues behind. Researchers were able to create a malicious firmware image, which contained a reverse proxy to the camera. In this way, it became possible for a remote attacker to connect to the device. It is a fact that IoT devices are hard to target since the malware gets expelled as soon as the device reboots but enabling the camera with backdoor spying capabilities ensures that the malware stays there.
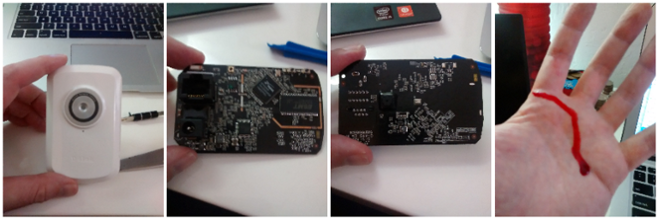
It was also identified during the research that it was possible to remove the firmware’s re-flash feature so that the camera owner cannot install firmware updates. The experiment was conducted on a $30 camera, which broke down on the desk of the researchers.
Cover Your Cams: Webcam of This Couple Got Hacked While Watching Netflix
Canadian Woman Hacker Arrested for spying on people through webcams
Apart from spying on the victims, webcam hacking has other advantages too. It makes stealing data easier since persistent backdoor into bounded networks through a web camera cannot be identified by security staff as the focus on servers and workstations.
Technically, the webcam offers limited versatility in terms of hardware or software exploitation. However, researchers believe that it could prove to be an entry point for attacks in future if not the main weapon of the attackers.
Vectra
Maydan