The hacker behind the data leak claims they downloaded the Raychat app data when the company exposed its entire database online between December 2020 to January 2021.
Raychat app (Raychat.io), a popular Iranian social and business messaging platform has apparently suffered a data breach in which personal data and records of over 150 million users have been leaked online.
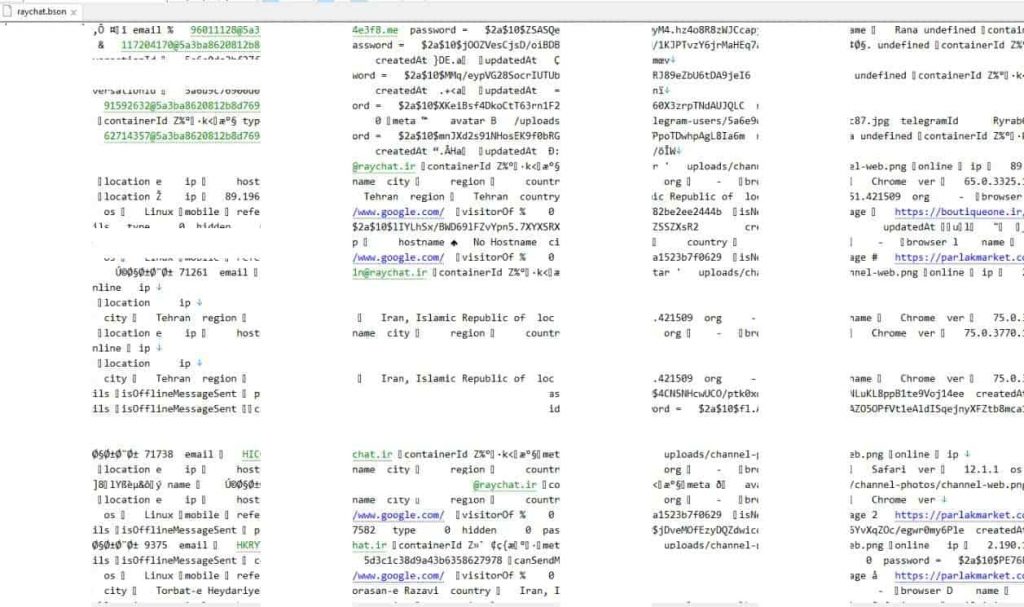
The data leak which has been seen and analyzed by Hackread.com includes:
Full names
IP addresses
Email addresses (The exact number leaked email address is yet unclear)
Bcrypt passwords
Telegram messenger IDs, etc.
Once upon a time in January 2021
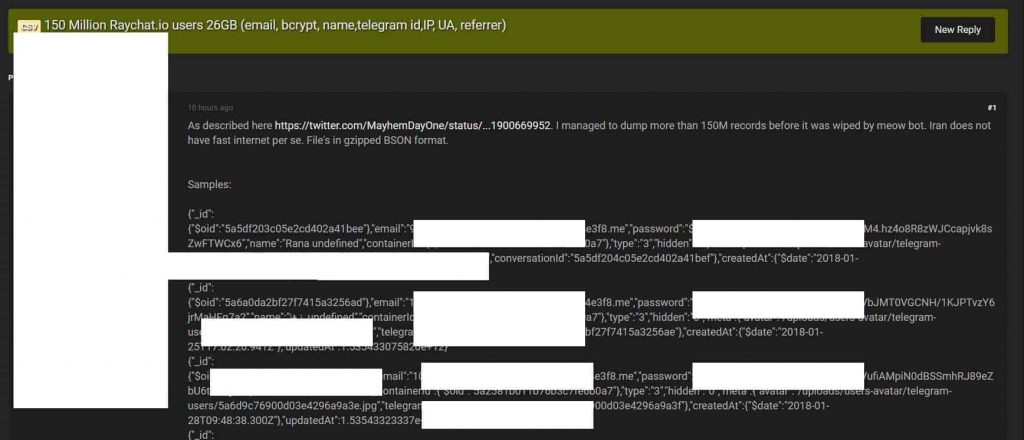
It is worth noting that the database first appeared on a popular Russian hacker forum around 7:20 AM, Monday, May 3, 2021. However, it is unclear whether the Raychat app had these records stolen from its servers or it was a result of a previous data leak that took place as a result of the misconfigured database identified by IT security researchers Bob Diachenko on January 31st, 2021.
SEE: Hacker dumps sensitive household records of 250M Americans
For your information, on January 31st, 2021, Diachenko tweeted that the Raychat app exposed its entire database on a misconfigured server. According to the researcher, the database contained more than 267 million accounts with data like names, emails, passwords, metadata, encrypted chats, etc.
Diachenko further added that the database was destroyed by a bot attack, referring to the meow attack, which appears to exist only to destroy databases that are misconfigured and exposed online to public access without any security authentication. The attack does not ensue any ransom notes or threats but just the word ‘meow’ along with a random set of numbers.
Diachenko had also revealed that he did not receive any response from the company. However, an Iranian Twitter user responded to the researcher with a screenshot apparently a tweet from the Raychat app stating there was no such data leak.

On the other hand, on Raid Forums that happened to be a prominent hacker forum, a threat actor took credit for the leak and claimed they downloaded the data before it was wiped out by the meow attack.
Nevertheless, Hackread.com’s analysis can confirm that the data seems quite authentic and puts the privacy of millions of Iranians in and out of the country at risk.
Iran and data breaches
Although Iranian hackers are pointed out for highly sophisticated attacks against their rivals, Iranian citizens are one of the biggest forgotten victims of data breaches in the last couple of years. For instance, in April 2019, a database, reportedly belonging to the Snapp app (Iranian Uber) leaked “astonishingly sensitive information” of millions of users on an insecure MongoDB server.
In April 2020, 52,000 Iranian ID cards with selfies were sold on the dark web and later leaked on the normal web.
In March 2020, the personal details and phone numbers of 42 million Iranians sold on a hacking forum. The database was initially exposed on a misconfigured database hosted on an Elasticsearch server.
A word of advice to Iranians
If you are on the Raychat app, it is the right time to get in touch with the company and inquire about the data breach. Additionally, watch out for phishing scams including fake emails from threat actors pretending to represent the Raychat app.
Moreover, since the data contains phone numbers you can also face SMSishing attacks that can drop malware to compromise your smartphone device.
Did you enjoy reading this article? Do like our page on Facebook and follow us on Twitter.
