Distributing malware through software updates of legit services is a tried and tested technique. We have reported countless such incidents where unsuspecting users were lured into installing the latest update or new version of the Adobe Flash Player. But, this time around, cyber criminals have added a little bit of innovation in their method.
According to Kaspersky Lab’s cybersecurity researchers, cybercriminals are using website security certificates to trap innocent users, and have infected a large number of websites with malware. When a user visits an infected site, a message is displayed stating that the website’s security certificate has expired and an update is necessary. This update is actually infected with either Mokes or Buerak malware.
Mokes is a sophisticated backdoor that can infect macOS and Windows systems and can perform a variety of functions including taking screenshots, executing codes, and stealing sensitive personal data from the device including audio and video files, documents, and PC information. Moreover, it uses AES-256 encryption to stay undetected and also installs another backdoor to increase persistence.
See: Hackers clone ProtonVPN website to drop password stealer malware
Buerak, conversely, infects Windows-based systems. This Trojan can manipulate running processes, execute code, steal data, increase persistence using registry keys, and also identifies different sandboxing and analytical mechanisms.
In a blog post, researchers explained that to trap the victims, the compromised websites display an error asking the user to update the SSL/TLS security certificates, which are website security certificates issued by Certificate Authorities to ensure encrypted communication between a browser and server, and prove the domain’s reliability.
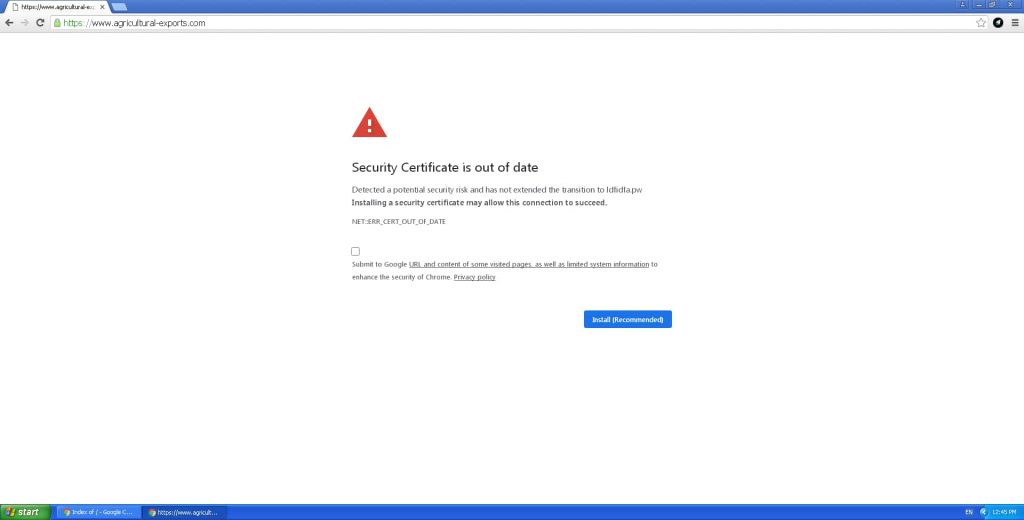
The message is displayed via an iframe in jquery.js script and the activity is monitored through a C&C server. When the user clicks on the update button, Certificate_Update_v02.2020.exe gets downloaded. Once it is installed, one of the two malware gets delivered to the computer.
According to the researchers, cybercriminals have infected a very diverse range of websites to lure a maximum number of users such as auto parts selling websites and zoos, etc. The infection was detected for the first time on January 16, 2020.
If you are on the Internet you need to be sure you don’t fall for such scams. To protect yourself, make sure you have a trustworthy anti-virus installed at all times, your system is upgraded to the latest version, your browser is equipped with a security plugin/extension that scans and warn of the website you visit. If you are still in doubt, use VirusTotal to scan a malicious URL.
Did you enjoy reading this article? Like our page on Facebook and follow us on Twitter.
