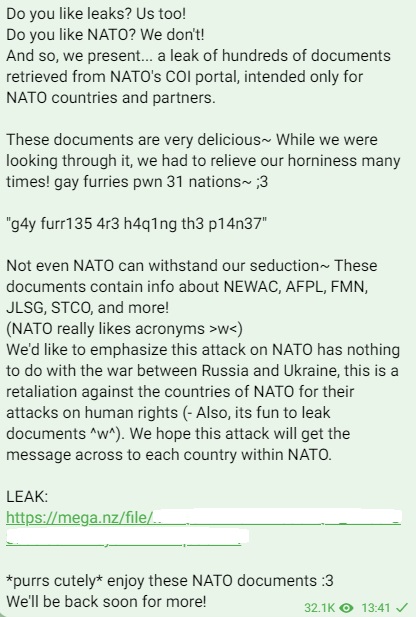
On its Telegram channel, the SiegedSec group claimed that its NATO hack has nothing to do with the war between Russia and Ukraine, and it is merely highlighting human rights abuses by NATO.
The hacktivist group “SiegedSec” has launched a cyber attack on NATO, claiming to compromise its COI portal and subsequently leaking hundreds of sensitive documents intended for NATO countries and partners. The data also contains full names, email addresses, phone numbers, office addresses, and ranks of at least 70 NATO officials.
This latest attack showcases the group’s increasing aggression and proficiency in breaching high-profile targets.
SiegedSec has emerged as a significant cyber threat, driven by a blend of hacktivism and personal gain, aiming to draw attention to its causes and also to exploit the momentum of offensive cyber operations for its own sinister objectives.
The motive behind the NATO hack, as claimed by SiegedSec, is the alleged infringement on human rights by NATO. While some may draw connections to Russia’s invasion of Ukraine and the subsequent rise of such threat groups, SiegedSec asserts that its attack on NATO is an act of retaliation against the countries of NATO for what they perceive as attacks on human rights.
Cyberint, a renowned cybersecurity research firm, has been closely monitoring SiegedSec’s activities and shared an exclusive report with Hackead.com detailing the group’s modus operandi. The group uses the Anonymous movement to carry out its attack, often referred to as a specialized “special forces unit” within the hacktivist landscape.
The alleged attack on NATO’s COI portal signifies a disturbing escalation in SiegedSec’s tactics. Their strategy often involves stealing and leaking sensitive information from well-known and popular companies or organizations to garner attention and gain free publicity. This tactic has proved effective in the past, evident from their high-profile campaign against Atlassian earlier this year.
Although NATO officials are yet to confirm the data breach, the leaked documents are said to contain information of critical importance to NATO countries and partners, raising concerns about potential security implications.
This is not the first time that NATO has been targeted by hackers. Earlier in April this year, the pro-Russian hacktivist group Killnet claims it carried out cyberattacks that resulted in the “paralysis” of 40% of NATO’s electronic infrastructure.
KillNet hackers also claimed that it targeted NATO with DDoS attacks, stole plain-text login credentials and used them to create accounts on a gay dating portal in Kyiv and Moldova.
RELATED ARTICLES
- NATO Data Stolen in Cyberattack on Portugal’s Armed Forces
- NATO Probes Hackers Selling Data from Top Missile Firm MBDA
- Authentication bypass flaw found in NATO, EU-approved firewall
- Smartphones of NATO Soldiers Compromised By Russian Hackers
- RomCom RAT Hits Pro-Ukraine Guests at Upcoming NATO Summit