An Australian security researcher Troy Hunt has identified a hidden security vulnerability that lets anyone monitor personal data including pictures and record voices of kids who use CloudPets toys. Needless to mention, if the information lands into the hands of malicious cyber-criminals, it could very well be used for raking in ransom.
It must be noted that CloudPets toys can be connected to mobile applications. These let parents and family members send messages to the kids, which are then played by the stuffed toys like teddy bears. To do this, you need to register at CloudPets by creating an account and provide the name of the kid and his/her picture along with an email address. The data is stored in the cloud instead of your smartphone on which the app is installed. CloudPets toys were launched in 2015. The all-animal range of toys includes rabbits, cats, dogs and stuffed bears.
More: After Spying Webcams, Welcome the Spy Toys “My Friend Cayla and I-Que”
Hunt has compiled a full-fledge report on the vulnerability of CloudPets toys and stated that more than 820,000 user accounts have already been exposed including 2.2 million voice recordings.
“I suspect one of the things that will shock people is that they probably didn’t think through the fact that when you connect the teddy bear, your kid’s voices are sitting on an Amazon server,” stated Hunt.
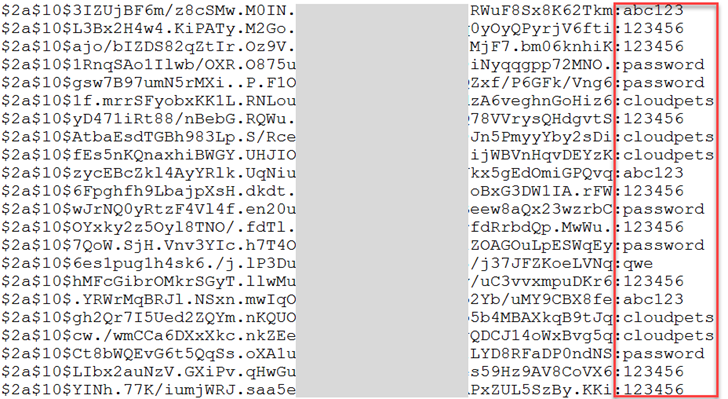
According to the findings, the central database of CloudPets’ voice messages and user related data was stored in a MongoDB server. The database was secured through basic hashes only, which protected user addresses and passwords. That’s why it wasn’t a difficult task for hackers to access the stored voice messages that are recorded from apps and toys since the same database was connected to the recordings.
The database was removed from the MongoDB server in January after demands for ransom started emerging using these recordings. Hunt believes that the company responsible for manufacturing these toys, the California-based Spiral Toys, didn’t have enough resources and finances to address the warnings and complaints from users. This particular database was also indexed by Shodan so you can check out if your kids’ toys are leaking data or not.
In one of the ransom attacks, the data was deleted by the attacker and a ransom note was uploaded after which CloudPets was required to pay the ransom in bitcoins. However, the company restored the lost data using the backup. The worst aspect is that the company didn’t inform users about the data leak as yet and the same passwords are being used until now. According to Californian law, companies need to notify users about such data breaches so, in that sense, we can term it as a clear violation of the law. It is also a matter of concern for parents as the Android app has already been downloaded over 100,000 times despite poor advertising and negative feedback from users.
Hunt was contacted by some concerned users about the vulnerability of CloudPets and Spiral Toys’ products citing that their emails are not being answered by the involved manufacturer firms. To get to the root of the matter, Hunt collaborated with tech website Motherboard’s reporter Lorenzo Franceschi-Bicchierai to report the issue to CloudPets but his efforts went in vain.
“Normally I would say get in touch with the company involved, but CloudPets is non-responsive. I almost think the advice here is to get in touch with local regulators and make a complaint about this,” said Hunt.
Hunt recommends that parents need to change the passwords in case they are reusing them somewhere else too. Already, it is not advisable to use the same password on various platforms.
Javvad Malik, security advocate at AlienVault and former 451 senior analyst at 451’s Enterprise Security Practice commented on the issue “A lot of the vulnerabilities and issues within children’s toys are a subset of the vulnerabilities we are seeing more of in the broader internet of things (IoT). With that in mind, the breaches of toys aren’t necessarily different. Any time you embed technology within a toy such as a doll, a kids tablet, a baby monitor, etc., particularly where there is external connectivity via internet or Bluetooth, you run the risk of someone accessing it inappropriately.
Shodan (the search engine for the internet of things) has a paid feed for members where they can trawl the internet to look for open webcams. Many show kids sleeping – as parents have them setup to monitor their children. It can also be searched for free at http://images.shodan.io/
Because security is a low priority for manufacturers and consumers, it typically doesn’t get implemented. So in theory, nearly any kids’ toy that has a camera and connectivity can be at risk.
What info is being stored:
A lot and poorly. Technology companies have an unhealthy fetish to collect as much data as possible. Whilst there are business benefits to knowing your customers – there needs to be a measure of appropriateness applied and the data that is collected needs to be properly secured.
Looking at the VTech breach, you had potentially millions of children’s details exposed. This included names, genders, birthdays, parents and home addresses amongst others. The questions that arise are, does a company really need that much information and are they protecting it adequately?
For the large majority of companies producing children’s toys, the answer is unfortunately, more likely to be a no on both accounts. Not only can you pinpoint individual children, such as John, age 8 who lives with his parents at this address, but it becomes relatively trivial to then steal a child’s identity – something that maybe won’t be discovered until the child is 18 and applies for their first bank loan or applies for a job – only to find they have been blacklisted on different systems.
What kind of risks are these toys creating for your entire family?
The internet today is not how it was 10-15 years ago. Letting all manner of devices and applications connect to the internet is, from a risk perspective, an unsustainable strategy. The sensitive nature of data transmitted via some of these toys, which can also include video or pictures of children – coupled with the fact that security is typically weak – it does indeed create another risk avenue. I’d say that yes, connecting to unsecured public wifi only increases the risk exposure.
Why would hackers want to breach kids’ toys anyway?
I am reminded of the story of the scorpion and the turtle, where the scorpion asks the turtle for a ride on its back across the river. Along the journey, the scorpion tries to sting the turtle on its shell. When the turtle asks why the scorpion acted in that way, the scorpion replied, “because it’s in my nature” (I hope you know the story I’m referring to, I’ve really shortened it).
Similarly, it’s in hackers’ nature to hack. If something has the technology, internet connectivity or something else – then a hacker will be curious in trying to determine how it works. The person who finds the vulnerability may not even be interested in exploiting it – but there are nefarious individuals that can use that knowledge to further their own goals.
Identity theft of children can be a particularly good avenue as it can provide returns long before it’s detected.
What should parents be doing to keep their children’s personal information safe?
We should teach kids, similar to the way we advise them not to accept candy from strangers or get into someone’s car. We need to become more aware of the dangers that are posed. Not sharing identifying information is the first step. Have a separate email account setup for registering toys. Don’t use your real name or address and don’t disclose details such as your school or where your parents work.
These tips could apply equally to many adults too. It only takes one member of the family to expose details that could undermine everyone’s privacy.”
More: UK May Approve Bill Allowing Spying on Individuals via Their Kids Toys
This is not the first time when a toy manufacturer has faced such a large scale data breach. In 2015, VTech, a Chinese firm faced a massive data breach in which 4.8 million parents and children details were stolen and leaked online.
Source: Troy Hunt
DDoS attacks are increasing, calculate the cost and probability of a DDoS attack on your business with this DDoS Downtime Cost Calculator.
