One of the world’s leading educational institution University College London (UCL) has come under a massive ransomware attack. According to reports, the attack affected the university’s IT system including student management system and shared drives.
The ransomware attack came weeks after the country’s National Health Service (NHS) had its IT system crippled by WannaCry ransomware attack. Although it is unclear what triggered WannaCry infection the authorities at UCL believe their system was infected through phishing emails containing malicious attachments or links.
UCL also believe that the attack could be a zero-day attack.
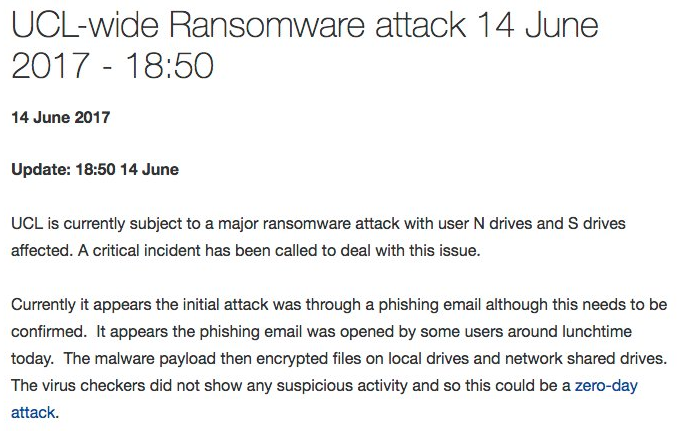
According to UCL’s security advisory:
“We wanted to provide a further update on the ransomware infection we are currently experiencing at UCL. We are continuing to investigate the infection that is affecting UCL users. Our current hypothesis is that the malware infection occurred through users visiting a website that had been compromised rather than being spread via email attachments. However, this remains unconfirmed at the moment.”
UCL, according to BBC is a “center of excellence in cybersecurity research.” This status was awarded by “The Government Communications Headquarters (GCHQ),” a British intelligence and security organization but according to UCL’s information services division “its virus checkers did not show any suspicious activity or catch the attack.”
The incident was first reported on Wednesday afternoon around 5 pm when UCL’s network and shared drives got infected. However, the University College London Hospitals associated with the NSH remained uninfected yet to protect it from the attack the authorities purposely suspended their NHS email system.
It is unclear what type of ransomware has targeted the UCL but the attack on its servers came the same day when Microsoft released a rare update to patch security flaws in its Windows OS to protect users from WannaCry like attacks.
Remember, WannaCry ransomware infection started from NHS hospitals and spread to more than 150 countries and affected 200,000 victims. The attack used NSA hacking tools leaked by ShadowBrokers hacking group. During the attack, the malware took advantage of SMB vulnerability in Windows.
As for the UCL attack, there’s more to come so stay tuned.
DDoS attacks are increasing, calculate the cost and probability of a DDoS attack on your business with this DDoS Downtime Cost Calculator.
