Another day, another Android malware – This time the malware spams users with advertisements and web links to generate revenue.
The IT security researchers at SophosLabs have discovered a new Android malware in seemingly harmless QR readers apps on Google Play Store. The malware has been developed to flood Android devices with large screen ads to generate revenue for attackers.
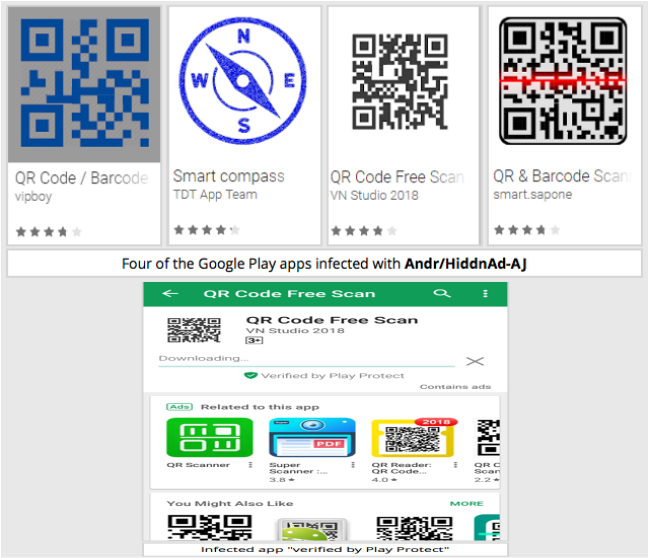
Dubbed Andr/HiddnAd-AJ by researchers, the malware was found in six QR code reading apps and one was in smart compass. All the infected apps made to Play Store by evading Google’s Play Protect, an app developed to intensify further the security of systems running on Android.
According to analysis, the malware works in such a way that once it infects the device, it waits up to six hours to start spamming the device with irritating large screen advertisements and notifications containing clickable links – All to generate as much revenue as possible.
“The adware part of each app was embedded in what looks at first sight like a standard Android programming library that was itself embedded in the app. By adding an innocent-looking “graphics” subcomponent to a collection of programming routines that you’d expect to find in a regular Android program, the adware engine inside the app is effectively hiding in plain sight,” wrote Paul Ducklin of SophosLabs.
More: 10 Powerful But Not Yet Promoted Antivirus for PC, Mac, Android, iPhone
At the time of publishing this article, the malware infected apps were reported to Google who did a quick job in removing the apps before further damage. However, some of the apps were already downloaded over 500,000 times.
If you have downloaded any of these apps, it is time to remove them right now. Moreover, the only safe place for Android users to look for clean apps is still Play Store, therefore, avoid downloading unnecessary apps. Sophos Labs also recommend sticking to Google Play if possible.
In addition, use an anti-malware app on your device, perform regular backups, scan it on regular bases and keep your operating system updated at all times.