Poland’s second largest telecom company Netia has suffered a data breach in which personal details of its users and clients have been leaked online!
A Ukrainian hacker going by the handle of Pravy Sektor has breached the servers of Poland’s telecom company Netia SA and stole a massive trove of data a couple of days ago and posted it for public access on an underground forum.

Netia SA has acknowledged that netia.pl
The attack was launched at 11:03 a.m. (0903 GMT) on Thursday and impeded access to Netia’s main web page netia.pl until late in the evening the same day, said spokeswoman Lidia Marcinkowska. She said hackers may have gained access to some data of its clients as they had accessed two types of forms sent via Netia’s website by people wanting to contact the company or sign a contract with it.
W związku z atakiem na naszą stronę informujemy, że serwisy, loginy, hasła do NOL są bezpieczne.Więcej informacji tu:https://t.co/Sdhhpqw05F
— NETIA SA (@NETIA_SA) July 9, 2016
Analysis:
The data was first discovered by Yogev Mizrahi, Head of cybersecurity team at Hacked-DB and analyzed by Oren Yaakobi who found the stolen data is far greater than what the company claims in their press releases. Here is a full and exclusive data analysis conducted by Hacked-DB:
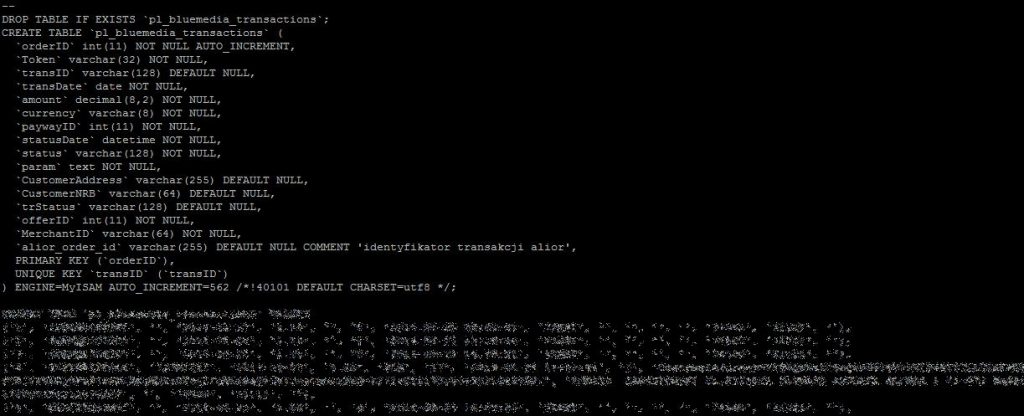
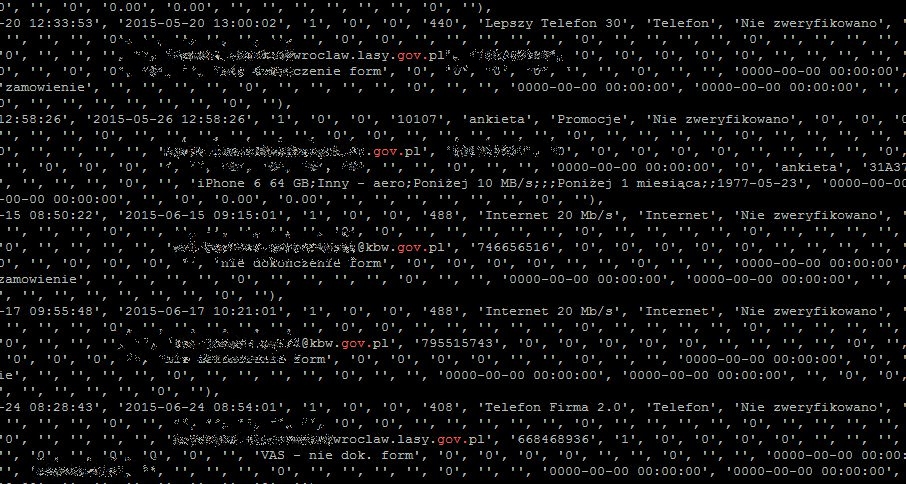
Ukrainian hacker posted multiple SQL files that are compromised and extracted from investor.netia.pl domain. There are several database files including sales DB that contains records such as Blue Media transactions, device and product offers, IP Block Lead and IP TradeDoubler. There’s also an SQL file containing 342,000 lines and contains data such as first and last name, home address and IP address. The data was last updated in 2014.
The leaked records also include data about clients and publication information such as email addresses, phone numbers, home address, IP details and full names. Another file in the database contains street address, city, area codes and IP addresses.
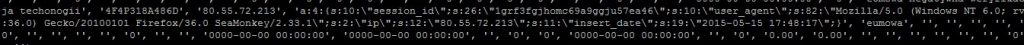
Researchers have also found a 9GB file size Log file containing, session ID, IP address, agent type, browser and the operating system details of users.
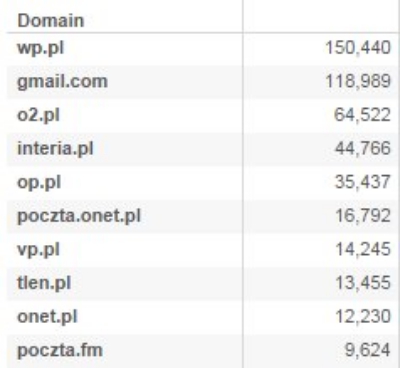
In total, the dumped data is about 14GB in size and last but not least, the hacker has also dumped 615,525 unique email addresses including 150,440 emails from Poland’s sixth-largest web portal Wirtualna, 118,989 Gmail emails addresses, 64,000 email address of O2 users. Here is a list of top 10 email domains compromised:
Recently, we have seen an increase in such offers where hackers have been offering highly confidential data from top social media giants including MySpace, LinkedIn, T
At the moment it is unclear what flaw allowed hackers to bypass Netia’s server but based on previous data breaches a simple SQL flaw lets hackers make their way to protected data. However, Netia’s website which was down after the attack has been restored. Here is a screenshot showing the site was down for maintenance: